Linux Distros for Cybersecurity
Protect your online privacy and security with the best Linux distros for cybersecurity. These distros come with built-in security features and tools to keep your data safe from hackers and cyber threats.
7 articles
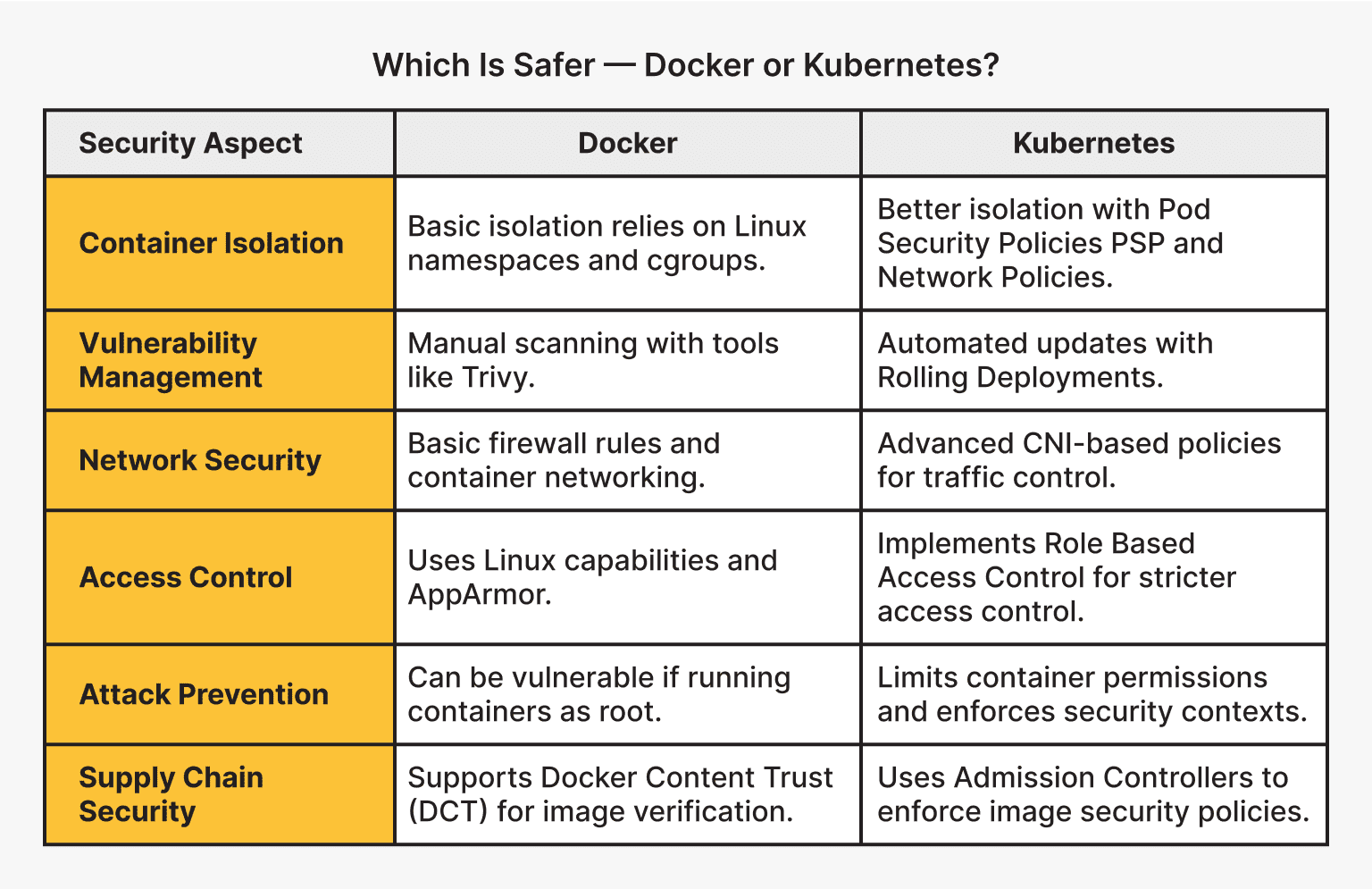
Linux Container Security: Docker and Kubernetes Best Practices for 2026
This article outlines best practices for securing Linux containers using Docker and Kubernetes, focusing on strategies for 2026 and beyond. It emphasizes a layered approach encompassing image security, orchestration safeguards, network policies, and runtime monitoring to protect against evolving threats. Prioritizing these practices is crucial for maintaining a robust and secure containerized environment.
2026-05-04 12:45:32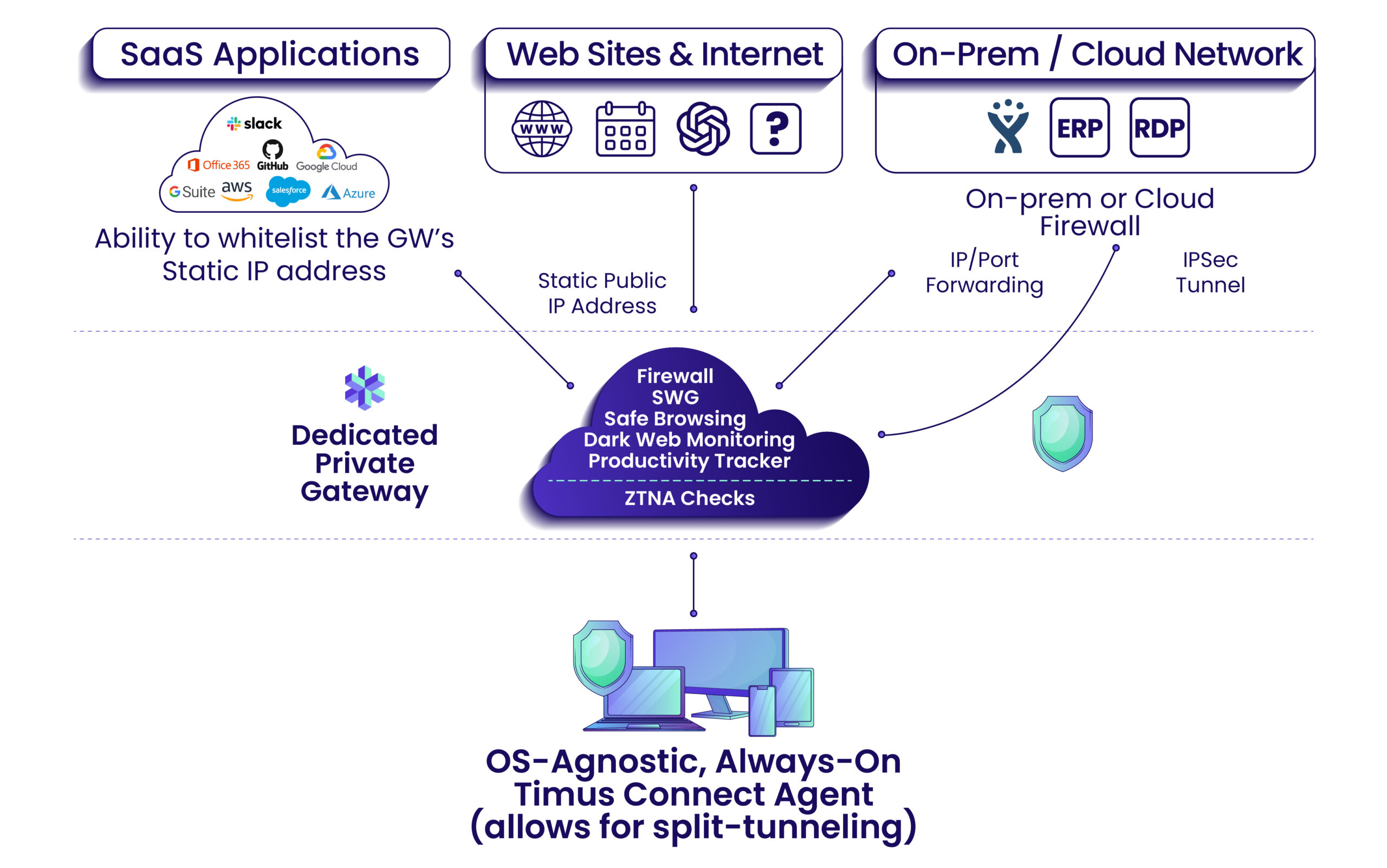
Zero Trust Network Management: Implementation Guide for Small to Medium Businesses in 2026
This guide details how small to medium businesses can implement a Zero Trust network architecture to bolster their cybersecurity posture. It emphasizes moving beyond traditional perimeter-based security to a 'never trust, always verify' model, focusing on identity verification, microsegmentation, and continuous monitoring. Successfully adopting Zero Trust minimizes risk and protects valuable business assets in today's evolving threat landscape.
2026-05-04 12:36:33
Quantum-Safe Cybersecurity: Essential Protection Strategies for 2026 and Beyond
The rise of quantum computing presents a looming threat to modern cybersecurity, potentially breaking widely used encryption algorithms. Organizations must begin preparing now by assessing their cryptographic infrastructure, exploring post-quantum cryptography solutions, and considering emerging technologies like Quantum Key Distribution to safeguard data in the quantum era.
2026-05-04 12:16:00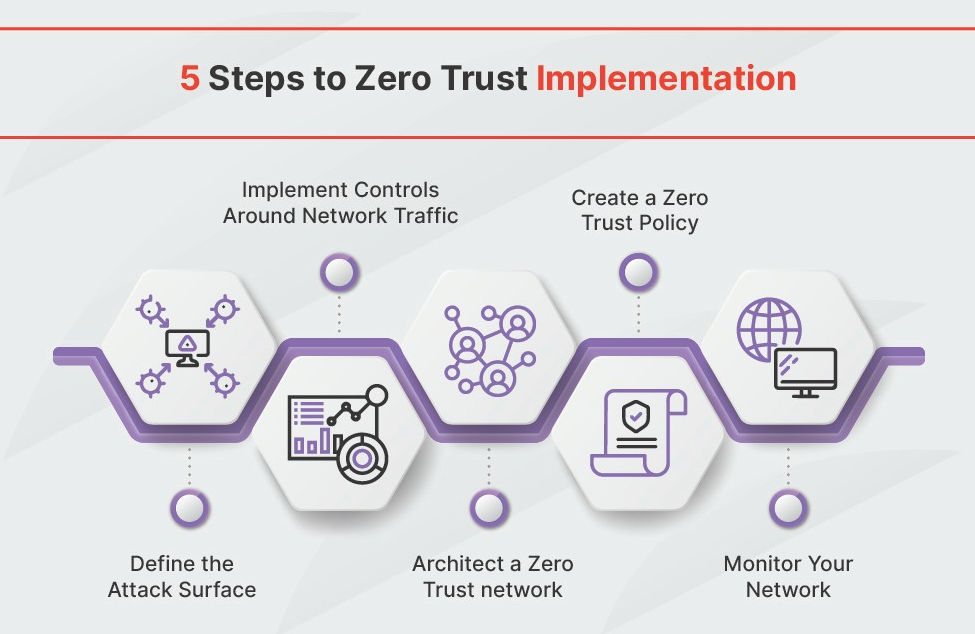
Zero Trust Network Architecture: Implementation Guide for 2026
This guide details the implementation of Zero Trust Network Architecture (ZTNA), a security framework designed for modern threats. It outlines the core principles of ZTNA, leveraging frameworks like NIST 800-207, and highlights the importance of microsegmentation, robust IAM, and data encryption. The guide advocates for a phased approach to implementation, ensuring a secure and manageable transition to a Zero Trust security posture.
2026-05-04 09:35:18
Quantum-Safe Cybersecurity: Essential Protection Strategies for 2026
The rise of quantum computing poses a significant threat to current encryption methods, necessitating a shift towards post-quantum cryptography. Organizations must begin assessing their vulnerabilities and planning a migration to NIST-standardized PQC algorithms to ensure long-term data security. This migration is complex and requires a phased approach, focusing on both software and hardware security.
2026-05-04 09:17:13
Post-Quantum Cryptography: Protecting Your Systems Against 2026 Cyber Threats
The rise of quantum computing threatens current encryption methods, necessitating a shift to post-quantum cryptography. NIST is leading the charge in standardizing new algorithms, particularly lattice-based approaches, to protect data in a post-quantum world. Organizations must begin preparing their systems now to avoid vulnerabilities as quantum computing capabilities advance.
2026-05-04 06:47:05
Zero Trust Network Security: Essential Cybersecurity Implementation Guide for 2026
Zero Trust Network Security is a modern cybersecurity framework that eliminates implicit trust and continuously verifies every user and device. This guide details the core principles, implementation steps, and benefits of adopting a Zero Trust architecture to protect against evolving cyber threats, particularly as organizations move towards cloud-based environments. It's a crucial shift for organizations seeking robust and adaptable security in 2026 and beyond.
2026-05-04 06:18:42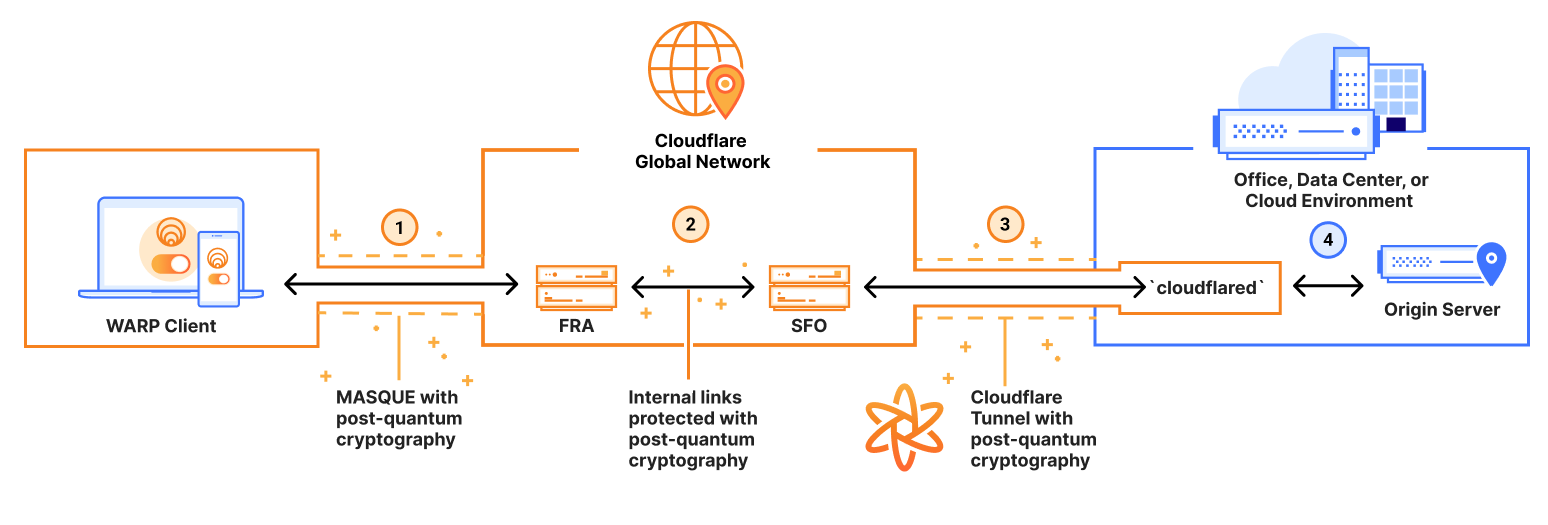
Quantum-Safe Cybersecurity: Preparing Your Network for Post-Quantum Threats in 2026
The rise of quantum computing poses a significant threat to current cybersecurity infrastructure. Organizations must begin preparing for this 'post-quantum' world by understanding their vulnerabilities and migrating to NIST-recommended, quantum-resistant cryptographic algorithms, with a target timeframe of 2026. Proactive planning and a phased approach are essential for a successful transition.
2026-05-04 03:36:42
Zero Trust Network Security: Essential Implementation Guide for 2026
Zero Trust Network Security is a modern approach to cybersecurity that moves beyond traditional perimeter-based defenses. It emphasizes verifying every user and device before granting access, regardless of location, and continuously monitoring for threats. Implementing Zero Trust is becoming essential for organizations to protect against evolving cyberattacks and prepare for the future of network security.
2026-05-04 03:15:59
Network Management for Remote Teams: 2026's Most Effective Tools and Techniques
Remote work is reshaping network demands, requiring organizations to adopt new tools and strategies for effective management. This article explores key technologies like SD-WAN, Zero Trust, and automation, alongside essential security best practices, to help teams navigate the complexities of distributed networks in 2026 and beyond. Successfully managing these networks ensures productivity, security, and a positive user experience for remote employees.
2026-05-04 00:25:40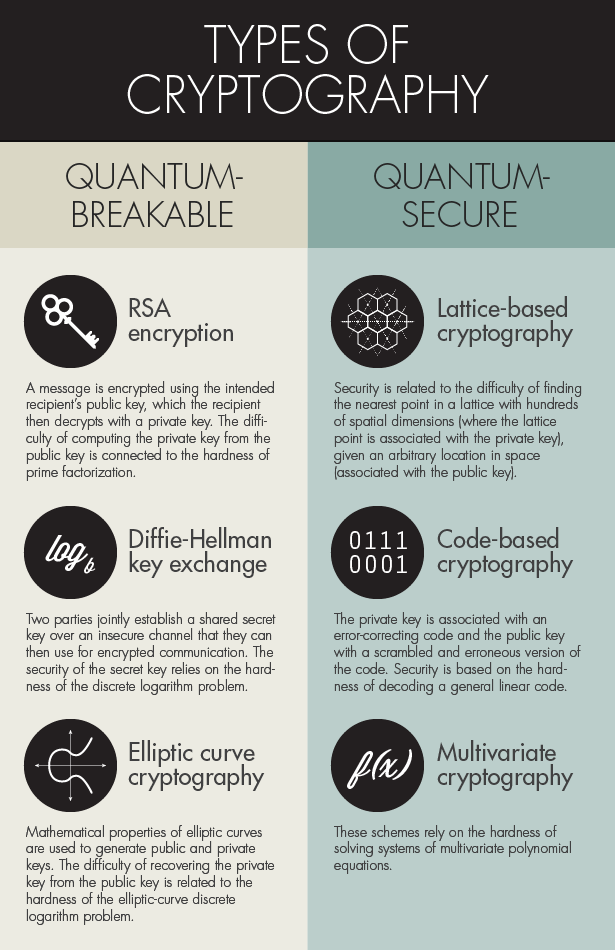
Quantum-Safe Cybersecurity: Essential Protection Strategies Every Tech Expert Needs in 2026
The emergence of quantum computing necessitates a shift in cybersecurity strategies. This article details essential steps tech experts should take by 2026, focusing on adopting post-quantum cryptography, leveraging hybrid encryption, and securing AI systems against quantum threats. Proactive preparation is crucial to maintain data security in a post-quantum world.
2026-05-04 00:16:36
Quantum-Safe Cybersecurity: Essential Protection Strategies for 2026 and Beyond
The emergence of quantum computing threatens to render current encryption methods obsolete, necessitating a shift to Post-Quantum Cryptography (PQC). This article outlines essential strategies for organizations to prepare for this transition, focusing on securing digital identities, protecting AI systems, and implementing robust network security measures. Proactive planning and a hybrid approach are crucial for navigating the evolving cybersecurity landscape.
2026-04-14 00:25:13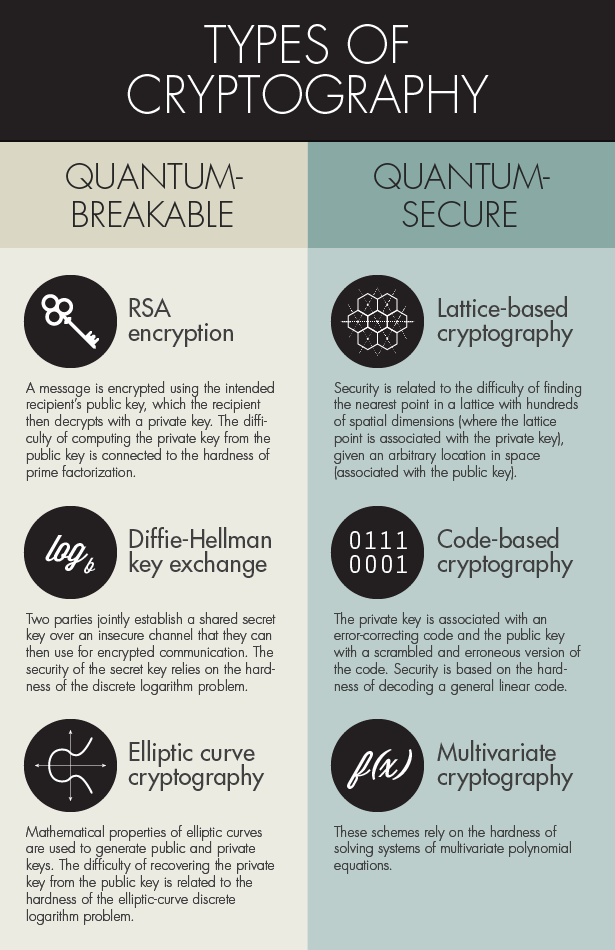
Quantum-Safe Cybersecurity: Essential Protection Strategies for 2026
The rise of quantum computing poses a significant threat to current cybersecurity infrastructure. Organizations must begin preparing now by understanding the quantum threat, exploring Post-Quantum Cryptography (PQC) solutions, and implementing a phased transition strategy to protect sensitive data. Staying informed about evolving standards and regulations is also critical.
2026-04-12 18:26:49
From Zero to Hero: A Comprehensive Guide to Arch Linux for Cybersecurity
Uncover the power of Arch Linux in cybersecurity with our detailed guide. Explore its unique features, learn how to set it up, and master best practices. Dive into the future trends of cybersecurity shaped by Arch Linux. Test your knowledge with our interactive quiz!
2023-08-28
A Comprehensive Guide to Arch Linux Security Best Practices and Tips
Explore Arch Linux security with our comprehensive guide, covering risks, best practices, and tips for enhanced protection. Learn to secure networks, user accounts, and utilize essential tools. Become an Arch Linux security expert today!
2023-08-12
Discover the Best Linux Distros for Cybersecurity: Enhancing Your System's Protection Against Threats
Explore top Linux distros for enhanced cybersecurity in this Guide Techy post. Learn factors to consider when choosing a distro & discover Kali Linux, Tails, Parrot Security OS, and Qubes OS. Boost your system's protection against threats today!
2023-06-11
A Showdown of Firewall Solutions: Comparing the Best Firewall Options for Arch Linux
Explore top firewall options for Arch Linux in this comprehensive guide. Learn their features, comparisons, and factors to consider for choosing the best solution. Master installation, configuration, and best practices.
2023-06-09