Welcome to the Fortress: Your Primer on Arch Linux Security 🔒
Welcome to the labyrinth of Arch Linux, a realm where security is the key that unlocks the door to untold potential. Arch Linux, a Linux distro celebrated for its simplicity, flexibility, and power, is a fortress that can be impregnable if you know how to harden its defenses. But why is linux distro security so pivotal?
Imagine your system as a castle. Without a well-fortified defense, it's an open invitation to marauders. From data breaches to system instability, the fallout can be catastrophic. A secure Arch Linux setup is your first line of defense, ensuring system stability and efficiency. Ready to delve into the world of Arch Linux security? Let this be your guide, your map to navigate the labyrinth of Arch Linux cybersecurity. Welcome to the fortress.

Behind the Curtain: Unraveling the Security Features of Linux 🔐
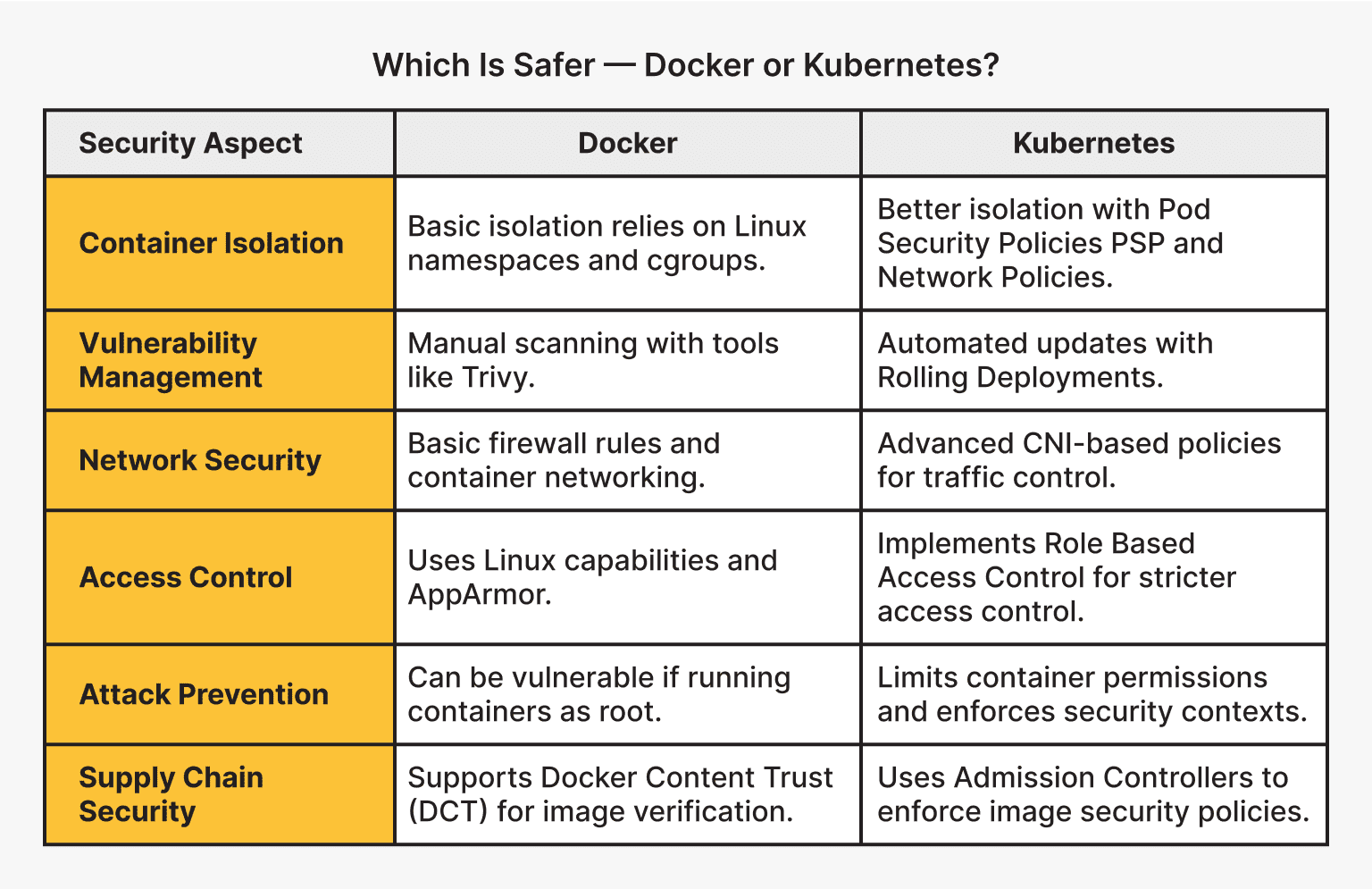
As we delve into the realm of Arch Linux security, we encounter a variety of robust features designed to fortify your system. SELinux, for instance, provides an advanced access control mechanism, allowing administrators to define precisely who can do what on your system. Similarly, AppArmor offers application-level security, confining programs to a limited set of resources. Firejail, on the other hand, is a sandboxing tool that isolates processes, limiting potential damage.
But what about Linux Security Modules (LSM)? Well, these are pluggable, stackable security modules that provide the foundation for much of the Linux security infrastructure, including SELinux and AppArmor. Understanding these security features is crucial for a secure Arch Linux setup. But how are these features implemented in Arch Linux? And what are the best practices for leveraging these tools for maximum security? Let's dig in and find out.
Guarding the Castle: Mastering Security Best Practices for Arch Linux 🛡️
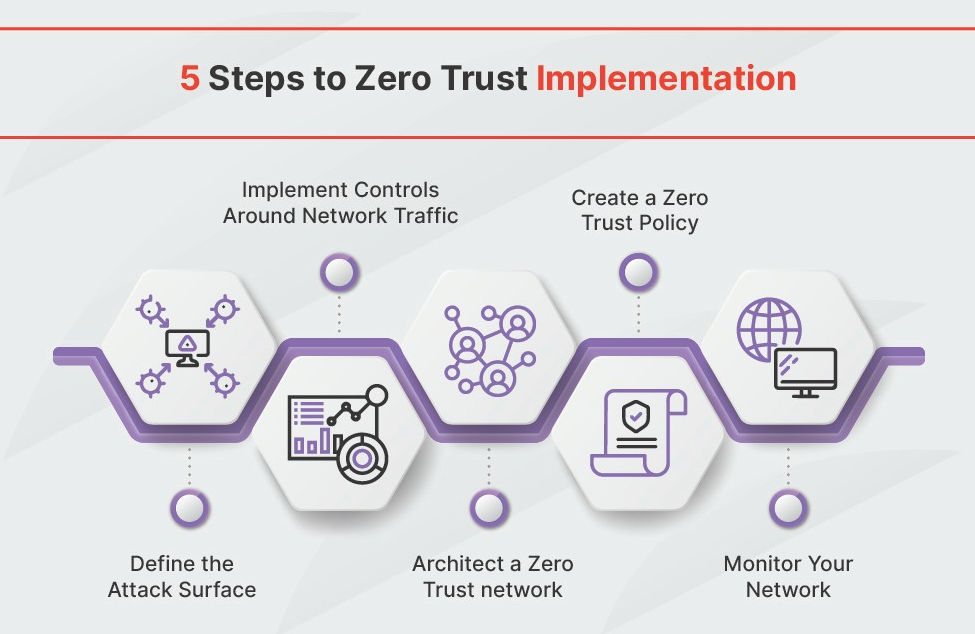
As you journey further into the world of Arch Linux, you'll realize that its security is a fortress that requires a vigilant gatekeeper. This is where Arch Linux hardening comes into play, a crucial aspect of Linux distro security. But how do you ensure a secure Arch Linux setup?
Firstly, it's essential to understand that security isn't a one-time setup - it's an ongoing commitment. It's about keeping your system updated, using strong passwords, and enabling firewalls. Sounds simple, right? Yet, these basic practices can sometimes be overlooked. But don't worry, we've got you covered with a checklist of these key practices and more in the upcoming sections.
Ready to dive deeper? Let's unravel the mysteries of Arch Linux security together. Remember, a secure system is not just about protection, it's about ensuring your system's stability and efficiency. Are you ready to be the vigilant gatekeeper?
Now that we've discussed the best security practices for Arch Linux, here's a handy checklist to help you implement them:
Great! You're on your way to a more secure Arch Linux system. Next, we'll delve into some advanced security tips.
Level Up! Advanced Security Wizardry for Arch Linux 🧙♂️
Delving deeper into the rabbit hole of Arch Linux security, we encounter a realm of advanced measures that safeguard your system like a fortress. System hardening, a pivotal part of this process, is akin to forging a sword; it strengthens your Arch Linux setup, making it resilient against potential threats. Our comprehensive guide can help you navigate this process.
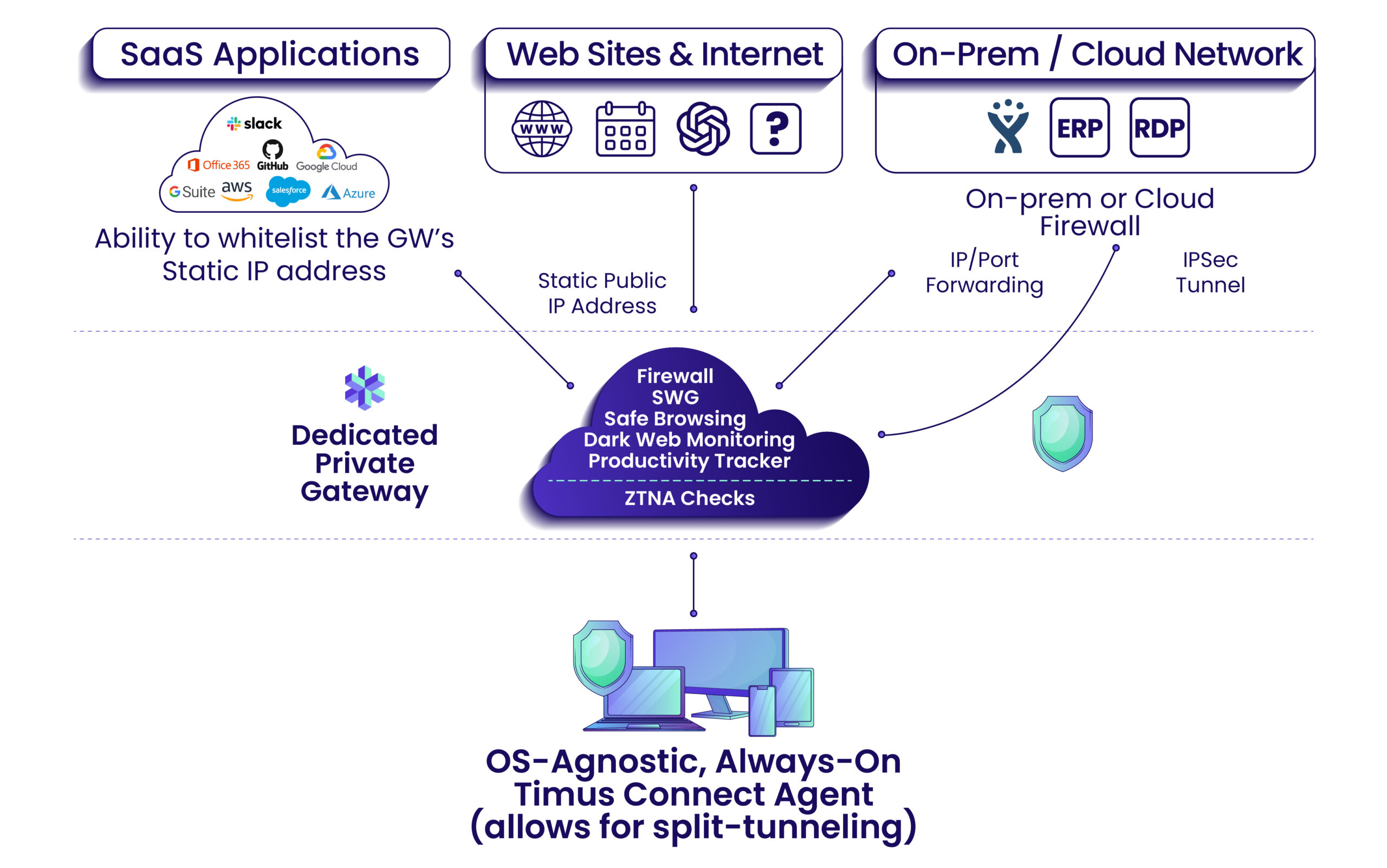
But what about the unseen invaders lurking in the network shadows? That's where network security comes into play, a shield against these invisible adversaries. Choosing the right firewall is crucial in this battlefield.
Lastly, let's not forget about SSH. This secure shell is your secret passage, ensuring safe and encrypted communications. But how can you make the most of it? Stay tuned for some handy tips and code snippets to elevate your Arch Linux security game!
Configuring SSH for Enhanced Security
Let's start with SSH (Secure Shell) configuration. SSH is a protocol used to securely log onto remote systems. We can enhance its security by modifying the SSH daemon configuration file, typically found at '/etc/ssh/sshd_config'. Here's a sample configuration:
# Disable root login
PermitRootLogin no
# Enable public key authentication
PubkeyAuthentication yes
# Specify the allowed users
AllowUsers user1 user2
# Change the default port
Port 2222
# Limit the number of authentication attempts
MaxAuthTries 3
# Enable two-factor authentication
AuthenticationMethods publickey,password publickey,keyboard-interactiveIn this configuration, we have disabled root login, enabled public key authentication, specified allowed users, changed the default port, limited the number of authentication attempts, and enabled two-factor authentication. Remember to replace 'user1' and 'user2' with your actual usernames. After making these changes, don't forget to restart the SSH service for the changes to take effect.
Oops! Troubleshooting Common Security Hiccups in Arch Linux 🚨
So you've had a taste of the common security hiccups in Arch Linux. Now, let's delve into the nitty-gritty of troubleshooting these issues. Picture this: you've just finished a fresh Arch Linux installation, but something feels off. Maybe your system is acting sluggish, or perhaps you've noticed suspicious network activity. Could it be a security issue? It's time to put on your detective hat and get to work.
First off, it's crucial to understand that no system, however secure, is invincible. Linux distros, including Arch, are no exception. But don't fret! With the right knowledge, you can turn your Arch Linux setup into a digital fortress. From identifying rogue processes to understanding the importance of regular system updates, we'll guide you through the process. Ready to embark on your Arch Linux cybersecurity journey? Let's roll!
Now that we've discussed common security issues and their solutions, you may have some questions. Here are some frequently asked questions about Arch Linux security:
We hope these answers have given you a deeper understanding of Arch Linux security. Remember, maintaining good security practices is an ongoing process. Let's conclude with some final thoughts.
The Final Word: Keeping Your Arch Linux Fortress Secure 🏰
Thus, we reach the end of this enlightening journey through the fortification of Arch Linux, but the quest for unyielding security is a never-ending one. A smooth sail in the turbulent waters of cybersecurity demands perpetual vigilance, an unwavering resolve to learn, and the will to adapt. Think of it as a fortress – always fortifying, always improving.
Remember, the best defense is a strong offense. So, why not dive deeper and master the art of network management? Or perhaps you're curious about how Arch Linux compares to other distros? If so, our Arch Linux vs Ubuntu comparison is a must-read.
So, what's your next move in this grand strategy of Arch Linux hardening? Will you be the guardian of your digital fortress, constantly vigilant and ready to adapt?
What's your key takeaway from our Arch Linux Security guide and what would you like to delve deeper into?
After reading our comprehensive guide on Arch Linux Security, we're curious to know what you've learned and what you're eager to explore further. Your feedback helps us provide more valuable content for you!



No comments yet. Be the first to share your thoughts!