The quantum threat
For decades, our digital security has rested on the assumption that certain mathematical problems are incredibly difficult for computers to solve. RSA and Elliptic Curve Cryptography (ECC) are prime examples – they’re used everywhere, from securing online transactions to protecting sensitive data. However, this foundation is about to be shaken. The advent of quantum computing poses a significant threat because these algorithms are vulnerable to a quantum algorithm called Shor’s algorithm.
Shor’s algorithm, developed by mathematician Peter Shor in 1994, can efficiently factor large numbers and solve the discrete logarithm problem – the very problems that RSA and ECC rely on for their security. While fully functional, large-scale quantum computers capable of running Shor’s algorithm don’t exist yet, the progress is accelerating. This isn’t a hypothetical future problem; it’s a looming crisis requiring urgent attention.
2026 is a target for many security teams. The G7 Cyber Expert Group released a roadmap on January 13, 2026, for moving to post-quantum cryptography. This date reflects how fast quantum hardware is moving and the years of work needed to swap out old encryption protocols.
The concept of 'Q-Day' – the moment a quantum computer can break current encryption – is a real concern. It’s not about predicting an exact date, but recognizing that once quantum computers reach a certain scale and stability, our current encryption will be compromised. Data encrypted today could be decrypted retroactively, making proactive preparation essential. Waiting until Q-Day arrives is simply too late; the transition to quantum-safe security is a multi-year undertaking.
Post-quantum cryptography algorithms
Post-quantum cryptography (PQC) is the standard way to fight quantum attacks. These algorithms work on normal computers but use math that quantum processors can't easily solve. We don't need new hardware or specialized physics for this, which makes it easier to deploy than other methods.
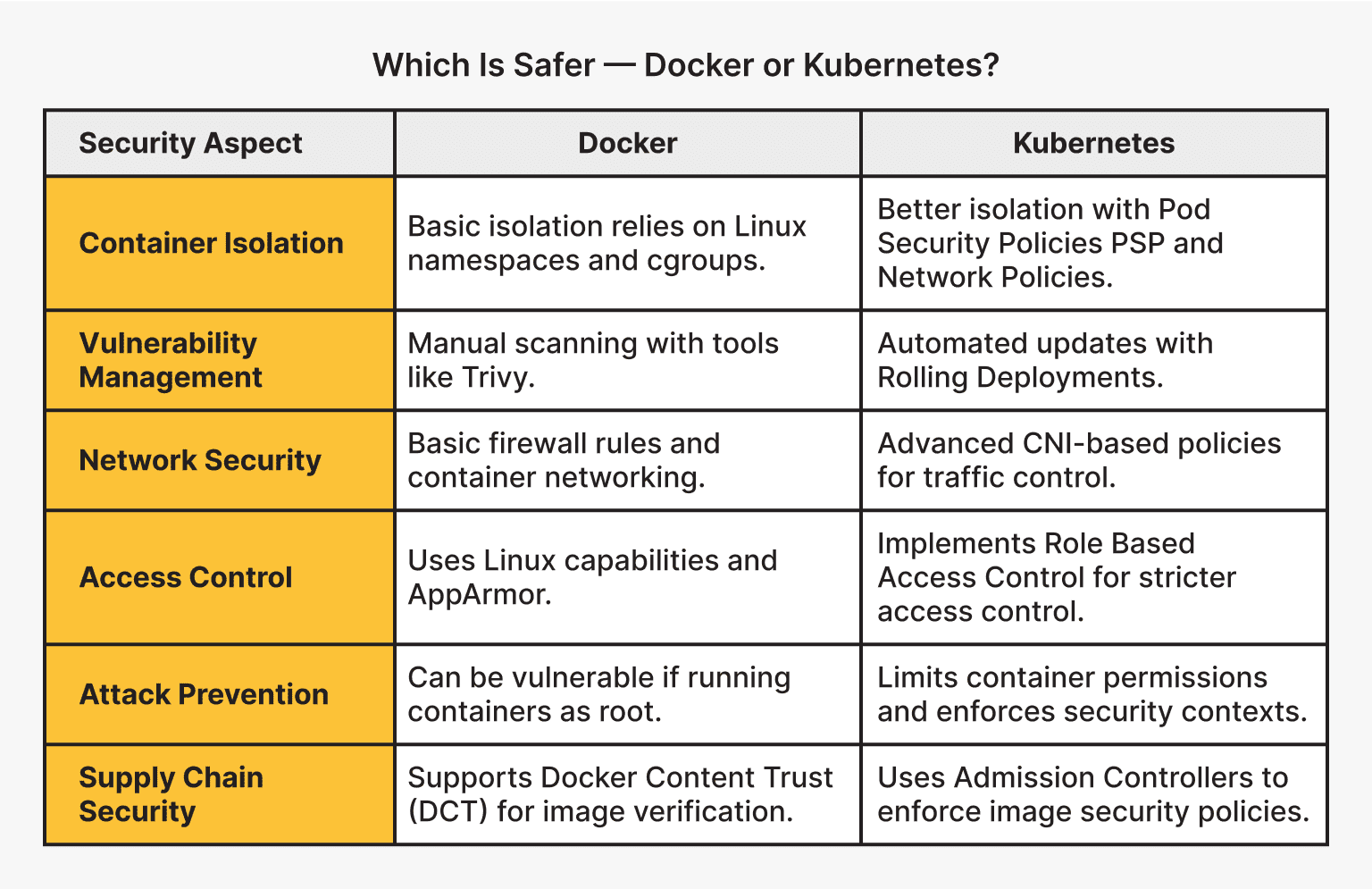
The National Institute of Standards and Technology (NIST) has been leading a standardization process to identify and validate PQC algorithms. In 2022, NIST announced the first set of algorithms selected for standardization: CRYSTALS-Kyber for key encapsulation, and CRYSTALS-Dilithium, FALCON, and SPHINCS+ for digital signatures. These algorithms represent a diverse range of approaches to PQC.
The selected algorithms fall into several categories. Lattice-based cryptography, like CRYSTALS-Kyber and CRYSTALS-Dilithium, relies on the difficulty of solving problems involving lattices. Code-based cryptography, like Classic McEliece (still under consideration), uses error-correcting codes. Multivariate cryptography, like Rainbow, is based on solving systems of multivariate polynomial equations, and hash-based signatures, like SPHINCS+, derive security from the properties of cryptographic hash functions.
Every algorithm has a downside. Lattice-based options are fast but use large keys. Hash-based signatures are secure but slow. We need 'algorithm agility'—the ability to swap one for another if a flaw appears. It's hard to build, but necessary if we want to avoid total system failure later.
- CRYSTALS-Kyber handles key encapsulation.
- CRYSTALS-Dilithium: Digital signature algorithm
- FALCON: Digital signature algorithm
- SPHINCS+: Digital signature algorithm
NIST Post-Quantum Cryptography (PQC) Algorithm Comparison
| Algorithm Name | Category | Key Size | Performance | Maturity |
|---|---|---|---|---|
| CRYSTALS-Kyber | Lattice-based | Moderate | Generally Fast | Well-studied |
| CRYSTALS-Dilithium | Lattice-based | Moderate | Good | Well-studied |
| Falcon | Lattice-based | Smaller | Fast signing, slower verification | Newer |
| SPHINCS+ | Hash-based | Larger | Slower | Well-studied, conservative design |
Qualitative comparison based on the article research brief. Confirm current product details in the official docs before making implementation choices.
How quantum key distribution works
Quantum Key Distribution (QKD) offers a fundamentally different approach to securing communications. Instead of relying on the computational hardness of mathematical problems, QKD leverages the laws of quantum physics to guarantee secure key exchange. The core idea is to transmit encryption keys encoded in the quantum states of photons.
Here's a simplified explanation: photons are polarized in different directions. Any attempt to eavesdrop on the transmission inevitably disturbs these quantum states, alerting the legitimate parties to the presence of an attacker. This inherent eavesdropping detection is a key feature of QKD, providing what’s known as information-theoretic security – security based on the laws of physics, not on assumptions about computational limitations.
QKD contrasts sharply with PQC. While PQC relies on the belief that certain mathematical problems will remain hard to solve even with quantum computers, QKD offers security regardless of advances in computing power. However, QKD isn’t a silver bullet. It has practical limitations, including distance restrictions due to signal loss, the high cost of implementation, and the need for dedicated infrastructure.
Companies like QNu Labs are actively developing QKD solutions. Their Armos product, for example, offers Quantum Key Distribution capabilities. While QKD is promising, it’s often viewed as a complementary technology to PQC, particularly for securing highly sensitive communications over limited distances.
Quantum random number generators
Cryptography relies heavily on randomness. Truly random numbers are essential for generating cryptographic keys, nonces, and other security-critical parameters. Traditional Pseudo-Random Number Generators (PRNGs), used in most software, are deterministic algorithms. This means that given the same seed value, they will always produce the same sequence of numbers, making them predictable and vulnerable to attack.
Quantum Random Number Generators (QRNGs) solve this problem by harnessing the inherent randomness of quantum phenomena. These devices exploit quantum processes – like the measurement of photon arrival times or quantum fluctuations – to generate truly random numbers. Because these processes are fundamentally unpredictable, the resulting numbers are cryptographically secure.
The benefits of using QRNGs are significant. They strengthen cryptographic keys, improve the security of random number-dependent algorithms, and enhance the overall robustness of security systems. QNu Labs’ Tropos product is an example of a QRNG solution, providing a source of high-quality random numbers for various security applications.
Adapting networks to quantum risks
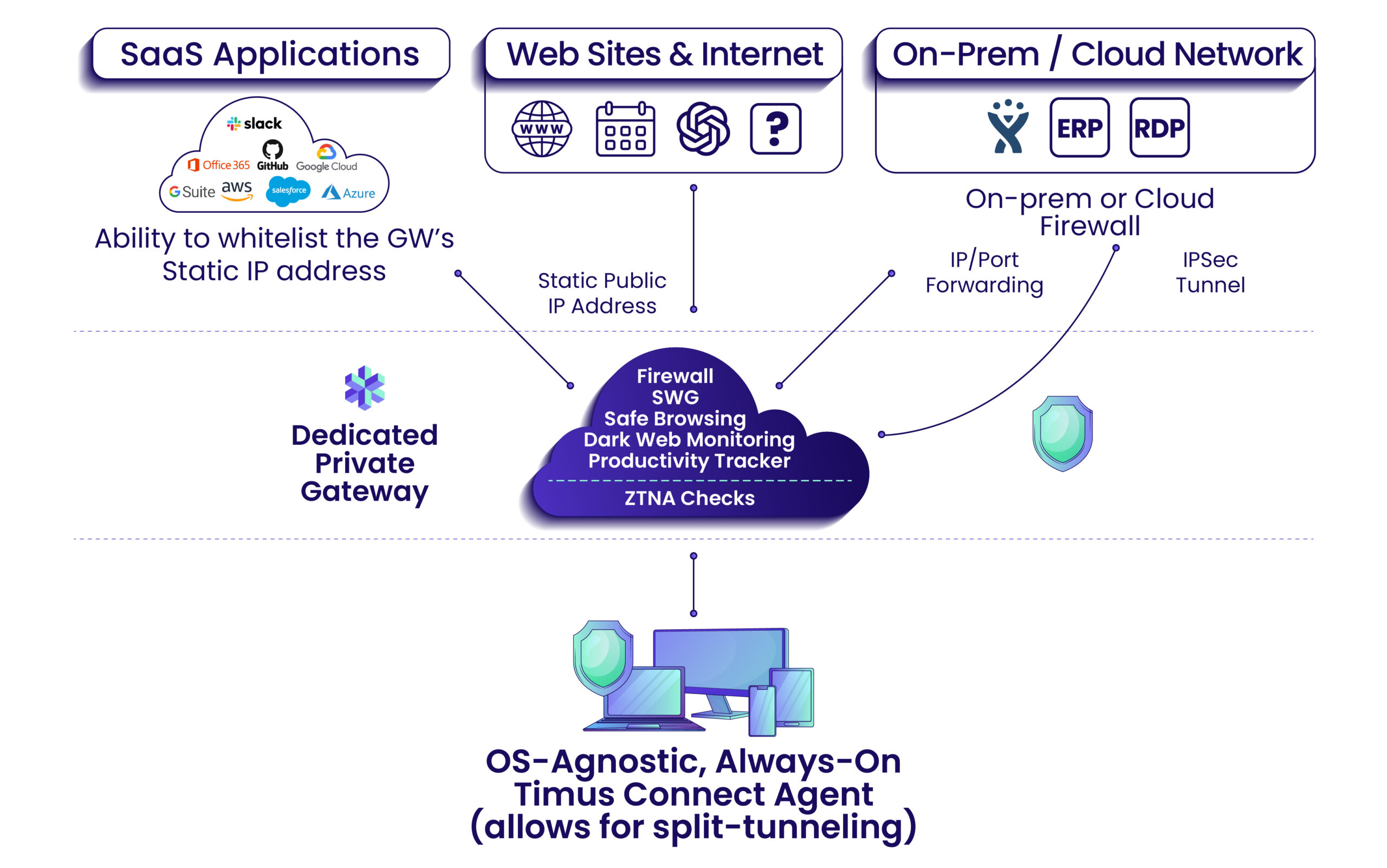
Protecting networks from quantum threats requires a comprehensive approach, starting with upgrading existing infrastructure. Virtual Private Networks (VPNs) and Transport Layer Security/Secure Sockets Layer (TLS/SSL) configurations – the foundations of secure network communication – need to be updated to support PQC algorithms. This means implementing new cryptographic libraries and protocols that incorporate the NIST-standardized PQC algorithms.
A hybrid approach is often recommended. This involves combining traditional encryption algorithms (like RSA and ECC) with PQC algorithms. This provides a layered defense, ensuring that even if one algorithm is compromised, the communication remains secure. The challenge lies in managing these hybrid systems and ensuring interoperability between different components.
Key management becomes even more critical in a quantum-safe world. Securely generating, storing, and distributing cryptographic keys is already a complex task; the introduction of PQC adds another layer of complexity. Organizations need to invest in robust key management systems that can handle the larger key sizes associated with some PQC algorithms.
Quantum-safe VPNs and secure tunnels, like QConnect offered by QNu Labs, are emerging solutions designed to protect network traffic from quantum attacks. These solutions typically leverage a combination of PQC algorithms and potentially QKD to provide a high level of security.
Quantum-resistant storage
Protecting data at rest – data stored on servers, in databases, and in the cloud – is equally important. The threat from quantum computers extends beyond communication channels; stored data encrypted with vulnerable algorithms can be decrypted retroactively once quantum computers become powerful enough.
Organizations need to re-encrypt existing data with PQC algorithms. This is a massive undertaking, particularly for large datasets. It requires careful planning, efficient algorithms, and potentially significant computing resources. Prioritizing data based on its sensitivity is a sensible approach.
The market is beginning to see the emergence of quantum-safe storage solutions. These solutions may involve hardware security modules (HSMs) that support PQC algorithms or cloud storage providers offering PQC encryption options. Qosmos, QVerse, and Q ORE Encryptor from QNu Labs are examples of potential solutions designed to secure data at rest against quantum attacks.
Migrating large datasets presents challenges. It’s not always feasible to re-encrypt everything immediately. A phased approach, focusing on the most critical data first, is often the most practical strategy.
Steps for 2026 readiness
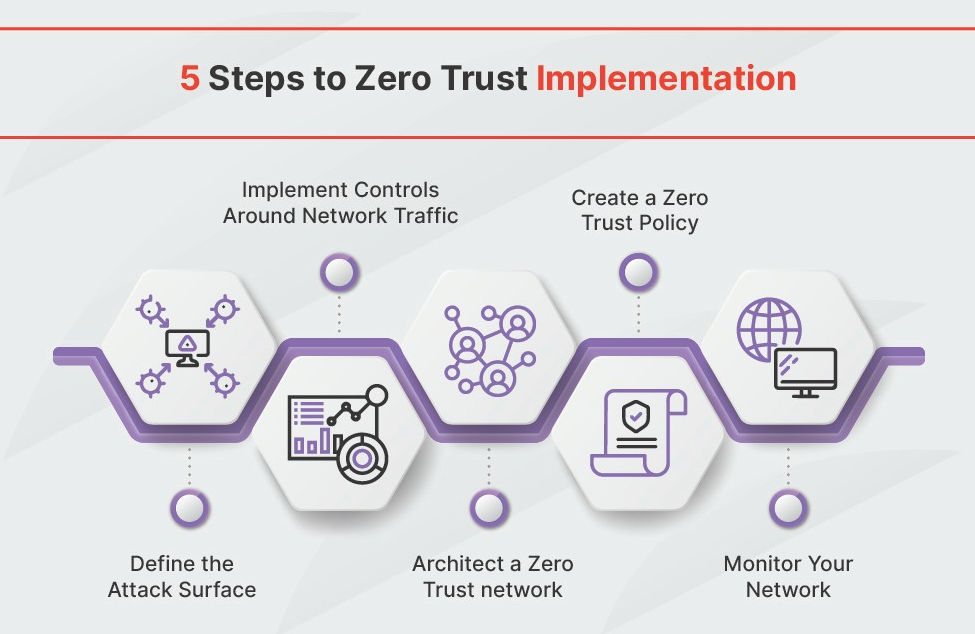
Preparing for the quantum threat requires a proactive and phased approach. Organizations should begin taking steps now, even if full implementation of quantum-safe security isn’t possible by 2026. Waiting until the last minute will be too late.
Here’s a practical checklist to guide your organization’s quantum readiness: First, inventory your cryptographic assets – identify all systems and applications that use encryption. Second, assess your quantum risk – determine which systems are most vulnerable and the potential impact of a quantum attack. Prioritize systems for upgrade based on this risk assessment.
Begin testing PQC implementations. Experiment with different algorithms and libraries to understand their performance characteristics and integration requirements. Develop a quantum-safe roadmap outlining the steps you will take to transition to PQC. Finally, train your security personnel on the principles of quantum cryptography and the implementation of PQC solutions.
Continuous monitoring and adaptation are crucial. The field of quantum cryptography is evolving rapidly. Stay informed about the latest developments and adjust your strategy accordingly. The transition to quantum-safe security is not a one-time project; it’s an ongoing process.
- List all systems and apps that use encryption today.
- Assess quantum risk
- Prioritize systems for upgrade
- Begin testing PQC implementations
- Develop a quantum-safe roadmap
- Train security personnel



No comments yet. Be the first to share your thoughts!