The quantum threat to encryption
For decades, our digital security has relied on the mathematical difficulty of certain problems. Specifically, algorithms like RSA and Elliptic Curve Cryptography (ECC) are the backbone of secure communication, protecting everything from online banking to government secrets. However, the emergence of quantum computing presents a serious challenge to this foundation.
Quantum computers leverage the principles of quantum mechanics to perform calculations far beyond the capabilities of even the most powerful classical computers. A key algorithm demonstrating this threat is Shor’s algorithm, developed by mathematician Peter Shor in 1994. This algorithm can efficiently factor large numbers – the core problem RSA relies on – and break ECC. The implications are substantial; if a sufficiently powerful quantum computer were built, much of our current encryption would become vulnerable.
I'm not sure anyone can give you a hard date for when RSA breaks. Most researchers I follow suggest we have a decade, but that's a guess. NIST is already finalizing new standards because swapping out encryption takes years. If you wait for the hardware to arrive, you've already lost.

New standards for post-quantum cryptography
Recognizing the potential threat, the National Institute of Standards and Technology (NIST) launched a standardization process in 2016 to identify and evaluate cryptographic algorithms resistant to attacks from both classical and quantum computers. This was a multi-year effort, involving submissions from cryptographers around the world and rigorous public review.
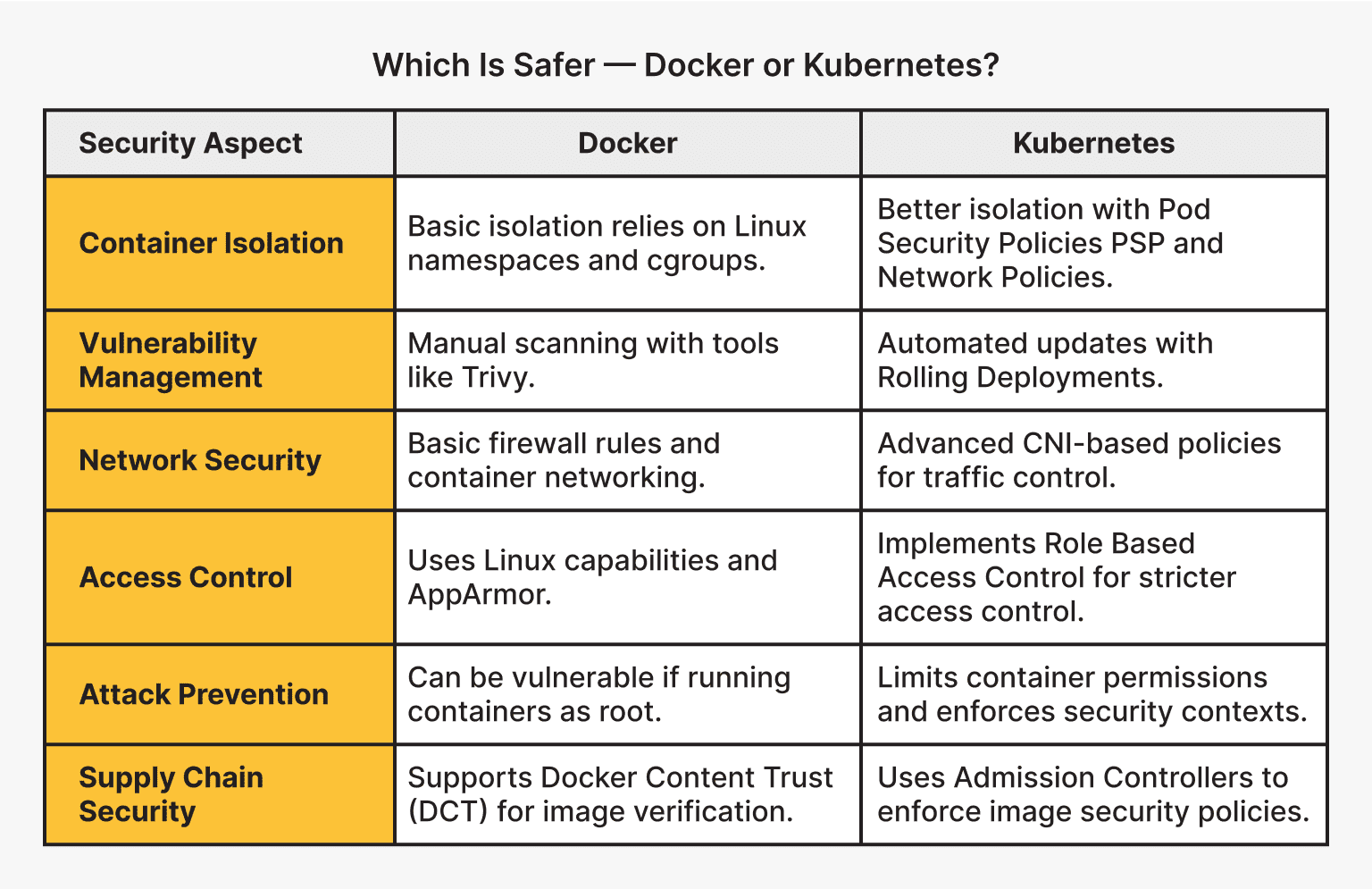
In 2022, NIST announced the first set of algorithms selected for standardization. These include CRYSTALS-Kyber for general-purpose encryption and key-establishment, CRYSTALS-Dilithium for digital signatures, FALCON for digital signatures (optimized for smaller signatures), and SPHINCS+ for digital signatures (offering a different security trade-off). Each algorithm is based on different mathematical problems. CRYSTALS-Kyber, for example, relies on the hardness of solving problems related to structured lattices.
These algorithms aren’t perfect. Different algorithms have different strengths and weaknesses in terms of speed, key size, and signature size. CRYSTALS-Kyber, for instance, is relatively fast but generates larger keys than some other options. SPHINCS+ is stateless, meaning it doesn’t require maintaining secret state, but it’s slower and produces larger signatures. The choice of which algorithm to use will depend on the specific application and its requirements.
The standardization process is ongoing. NIST continues to evaluate additional algorithms for potential future standardization. The goal is to provide a diverse set of options to meet the needs of different applications and ensure a robust and resilient cryptographic ecosystem. This isn't about replacing everything at once, but about preparing for a future where quantum computers are a factor.
- Kyber handles general encryption and is usually the fastest option.
- CRYSTALS-Dilithium: Digital signatures
- FALCON: Digital signatures (smaller size)
- SPHINCS+: Digital signatures (stateless)
NIST Post-Quantum Cryptography (PQC) Algorithm Comparison
| Algorithm Name | Function | Security Basis | Performance Profile | Implementation Difficulty |
|---|---|---|---|---|
| CRYSTALS-Kyber | Key Exchange | Lattice-based | Generally faster execution; Larger key sizes compared to some others. | Moderate |
| CRYSTALS-Dilithium | Digital Signature | Lattice-based | Good balance of signature size and verification speed. | Moderate |
| Falcon | Digital Signature | Lattice-based | Smaller signature sizes, potentially better for bandwidth-constrained environments. | Higher |
| SPHINCS+ | Digital Signature | Hash-based | Highly conservative security approach; Stateless signature scheme. | Moderate to High |
| Classic McEliece | Key Exchange | Code-based | Very large key sizes; Relatively fast encryption/decryption. | Higher |
Qualitative comparison based on the article research brief. Confirm current product details in the official docs before making implementation choices.
Finding your vulnerabilities
Before you can migrate to post-quantum cryptography, you need to understand your current cryptographic landscape. What encryption algorithms are currently in use within your organization? Where are they being used – to protect data in transit, data at rest, or to create digital signatures? Identifying these dependencies is the first step.
Start by inventorying the systems and applications that rely on cryptography. Pay close attention to those that use RSA or ECC, as these are the most vulnerable to quantum attacks. Consider the sensitivity of the data being protected; systems handling highly sensitive information should be prioritized for migration. A thorough understanding of your current infrastructure is essential.
CISA has a few checklists for this. Their guides help you spot where you're exposed, but a self-assessment only goes so far. You'll eventually need a professional audit to find the gaps you missed.
How to start the migration
Migrating to post-quantum cryptography is a complex undertaking, and a phased approach is generally recommended. A complete overhaul of all cryptographic systems at once is rarely feasible or practical. Instead, consider a hybrid approach, combining classical and quantum-resistant algorithms. This allows you to maintain compatibility with existing systems while gradually introducing quantum-resistant security.
Prioritization is key. Focus on systems that protect the most sensitive data or are considered critical to your operations. Systems handling long-lived data, like archived records, should be prioritized because they have a longer window of vulnerability. Begin with pilot projects to test and refine your migration strategy before deploying it more broadly.
Software and hardware upgrades will likely be necessary. Many existing cryptographic libraries and hardware security modules (HSMs) will need to be updated to support the new PQC algorithms. Key management is also crucial. Ensuring the secure generation, storage, and distribution of quantum-resistant keys is essential. This is a fundamental aspect of any cryptographic system.
Backwards compatibility is a significant challenge. You need to ensure that systems using PQC can still communicate with systems using classical cryptography. Hybrid approaches address this issue, but careful planning and testing are required. The transition will take time and effort, but it’s a necessary investment to protect against the future threat of quantum computers.
Securing networks
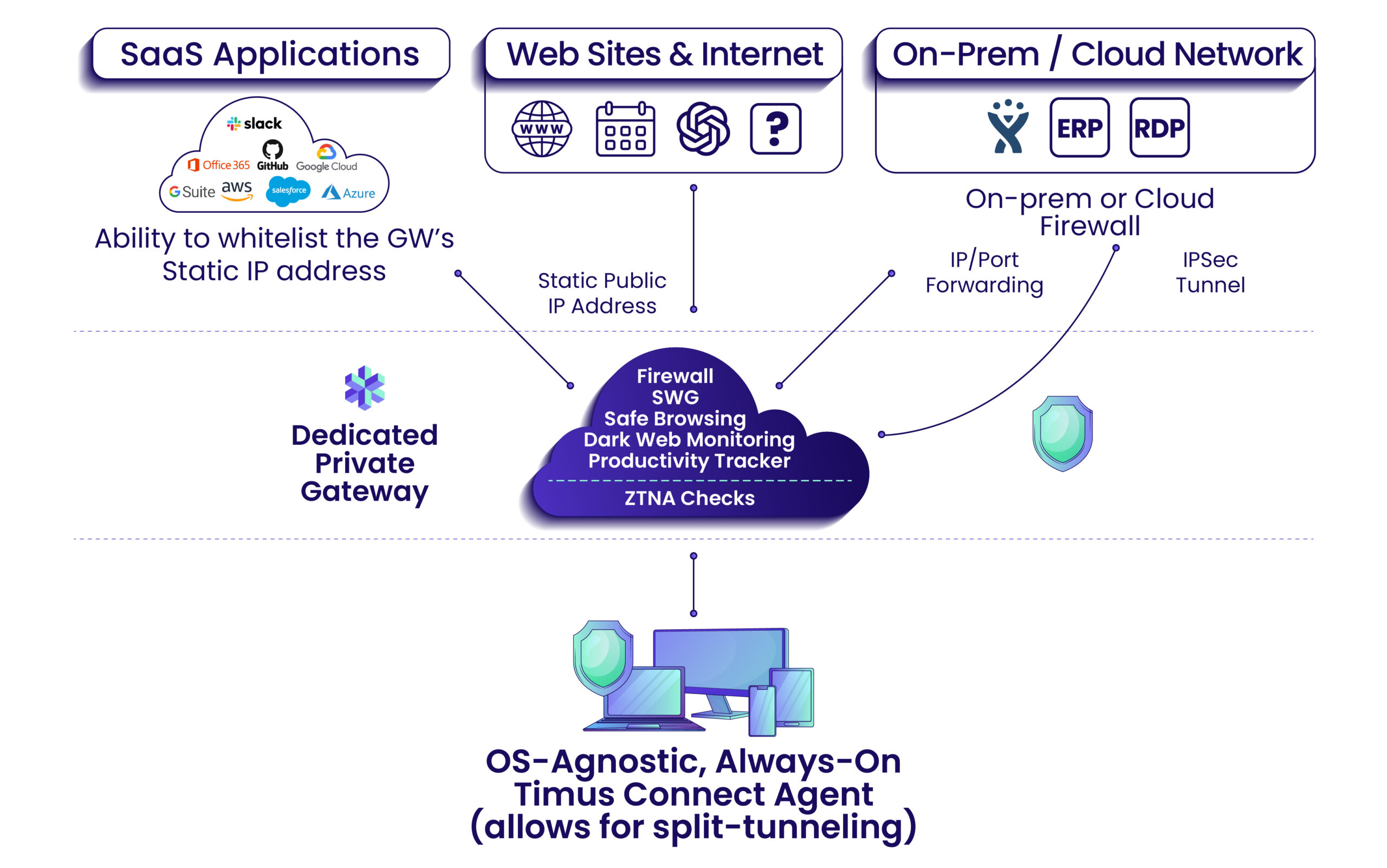
Quantum computing also impacts network security protocols. Protocols like TLS/SSL, SSH, and VPNs rely on encryption to protect data in transit. These protocols will need to be updated to incorporate quantum-resistant key exchange mechanisms. The good news is that these protocols are designed to be flexible and adaptable.
Quantum Key Distribution (QKD) is a potential solution, but it’s not without limitations. QKD uses the principles of quantum mechanics to securely distribute encryption keys. However, QKD requires specialized hardware and has limited range. It’s currently more suitable for securing point-to-point links than for large-scale network deployments.
Deploying QKD at scale presents significant challenges. The cost of the hardware, the limitations on distance, and the need for trusted infrastructure all pose obstacles. While QKD may play a role in securing critical infrastructure, it’s unlikely to be a complete solution for most organizations. The focus will likely be on integrating PQC algorithms into existing network protocols.
Moving towards quantum-resistant protocols requires careful planning and coordination. Updates to network devices, servers, and client software will be necessary. Regular security audits and penetration testing will be essential to ensure that the network remains secure in the face of evolving threats.
Resources and Further Learning
Staying informed is key to navigating the transition to quantum-safe security. Several resources provide valuable information and tools. The NIST Post-Quantum Cryptography website () is the central hub for information on the standardization process.
CISA provides cybersecurity guidance and resources for organizations of all sizes. Their website () offers a wealth of information on cybersecurity best practices. Academic papers and industry reports also provide valuable insights into the latest developments in quantum computing and PQC.
- The NIST PQC project page tracks the latest algorithm approvals.
- CISA Cybersecurity Guidance:
- PQClean:
- Open Quantum Safe:
Essential Resources
- NIST Post-Quantum Cryptography (PQC) Project - This initiative is standardizing new cryptographic algorithms resistant to attacks from quantum computers. It provides algorithm specifications and guidance for implementation.
- CISA Cybersecurity Best Practices - The Cybersecurity and Infrastructure Security Agency offers guidance on transitioning to post-quantum cryptography as part of broader cybersecurity improvements. Review their recommendations for a layered security approach.
- Open Quantum Safe (OQS) Project - This open-source project provides implementations of post-quantum cryptographic algorithms and tools for evaluating their performance and security. It focuses on integrating PQC into existing systems.
- PQShield - A company offering solutions for integrating post-quantum cryptography into TLS/SSL and other protocols. They provide tools for assessing quantum risk and implementing PQC algorithms.
- Academic Research on Lattice-based Cryptography - Explore papers detailing the security and efficiency of lattice-based algorithms, a leading candidate in the NIST PQC standardization process. Focus on recent publications from cryptography conferences.
- Research on Multivariate Cryptography - Investigate academic papers examining the strengths and weaknesses of multivariate cryptography, another family of algorithms under consideration by NIST.
- Code-based Cryptography Studies - Review current research on code-based cryptography, specifically focusing on the McEliece cryptosystem and its variants, which are also being evaluated for post-quantum security.


No comments yet. Be the first to share your thoughts!