The Looming Quantum Threat: Why Current Encryption Isn’t Enough
For decades, our digital security has relied on the mathematical difficulty of certain problems. Algorithms like RSA and ECC, which protect everything from online banking to government communications, are built on the idea that it would take an impossibly long time for even the most powerful computers to break them. But that’s changing. Quantum computing introduces a fundamentally different way of processing information, and it threatens to render these algorithms obsolete.
The core of the problem lies with Shor’s algorithm, developed by mathematician Peter Shor in 1994. This algorithm, designed to run on a quantum computer, can efficiently factor large numbers and compute discrete logarithms – the very problems that RSA and ECC rely on for their security. While a practical, fault-tolerant quantum computer capable of running Shor’s algorithm at scale doesn’t exist yet, the progress is accelerating.
The Cloud Security Alliance's 2023 survey suggests a 50% chance that quantum computers will crack RSA-2048 by 2030. A report from the Cybersecurity and Infrastructure Security Agency (CISA) emphasizes this urgency, stating that organizations need to begin preparing now. The timeline is uncertain, but the risk is permanent. The potential consequences of inaction are severe: compromised data, disrupted critical infrastructure, and a loss of trust in digital systems.
The threat isn't limited to future scenarios either. 'Harvest now, decrypt later' attacks are already a concern. Malicious actors are actively collecting encrypted data today, anticipating the day they can decrypt it with a future quantum computer. This makes proactive encryption a current priority.
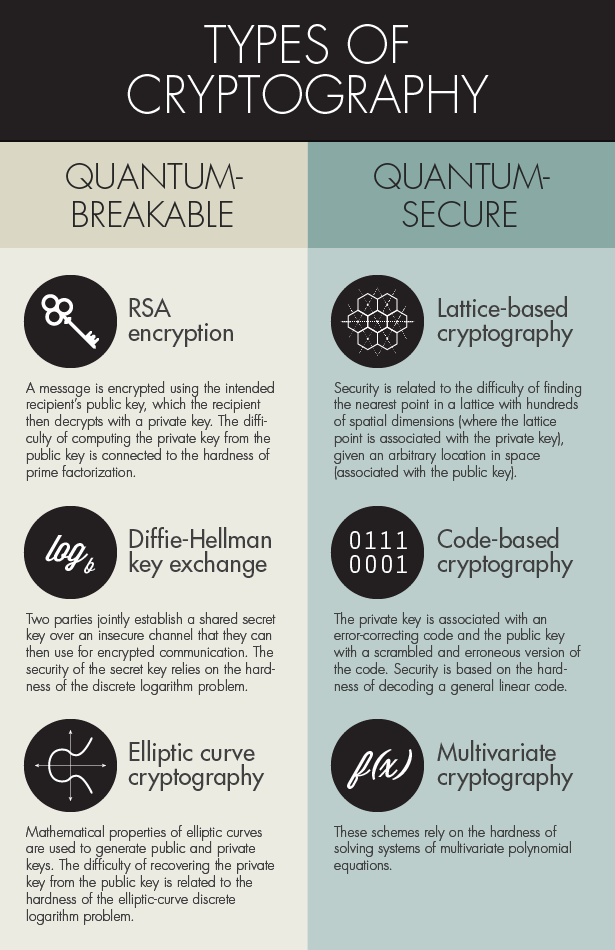
Post-Quantum Cryptography: The Algorithms Stepping Up
The response to the quantum threat is Post-Quantum Cryptography (PQC) – the development of cryptographic algorithms that are resistant to attacks from both classical and quantum computers. After a multi-year evaluation process, the National Institute of Standards and Technology (NIST) announced its first set of standardized PQC algorithms in 2022 and 2024.
The initial selections focus on two main categories: key encapsulation mechanisms (KEMs) and digital signatures. CRYSTALS-Kyber is the first KEM standard, designed to securely exchange encryption keys. For digital signatures, NIST selected four algorithms: CRYSTALS-Dilithium, Falcon, SPHINCS+, and a second round of algorithms is still in process. Each algorithm uses different mathematical problems to ensure security. Dilithium and Falcon are lattice-based. Their security is tied to the difficulty of solving shortest vector problems in high-dimensional grids.
SPHINCS+ takes a different approach, relying on hash functions. It's considered more conservative, as it doesn't depend on unproven assumptions about the hardness of mathematical problems. The algorithms that didn’t make the cut – like SIKE – were found to have vulnerabilities or weren't considered sufficiently mature. While promising, they require further research and development before they could be considered for standardization.
The choice of algorithm isn’t one-size-fits-all. Kyber is fast. Dilithium is more secure. Falcon is known for its smaller signature sizes, which can be beneficial in bandwidth-constrained environments. SPHINCS+ is slower but offers resilience against a wider range of potential attacks. Understanding these tradeoffs is crucial when selecting the right algorithm for a specific application.
NIST Post-Quantum Cryptography (PQC) Algorithm Comparison
| Algorithm Name | Key Size | Signature Size (where applicable) | Security Level (estimated against Grover's algorithm) | Computational Complexity | Strengths | Weaknesses |
|---|---|---|---|---|---|---|
| Kyber | Relatively small (e.g., Kyber768: 768 bytes public key, 256 bytes secret key) | N/A - Key Encapsulation Mechanism (KEM) | Estimated equivalent to AES-128/192/256 | Moderate – generally faster than other PQC candidates | Good performance characteristics; relatively small key and ciphertext sizes; suitable for a wide range of applications. | Performance can vary depending on implementation; potential vulnerabilities discovered and addressed in later versions. |
| Dilithium | Moderate (e.g., Dilithium3: 2560 bytes public key, 2560 bytes secret key) | 2048 - 13952 bytes (depending on parameter set) | Estimated equivalent to AES-128/192/256 | Moderate to High – slower than Kyber, but faster than Falcon and SPHINCS+ | Strong security proofs; relatively compact signatures compared to Falcon and SPHINCS+. | Larger key sizes than Kyber; signature generation and verification can be computationally intensive. |
| Falcon | Moderate (e.g., Falcon-512: 897 bytes public key, 1280 bytes secret key) | 690 - 1280 bytes (depending on parameter set) | Estimated equivalent to AES-128/192/256 | High – more computationally demanding than Kyber and Dilithium | Compact signatures; relatively fast signature verification. | Slower signature generation; more complex implementation; potential side-channel vulnerabilities require careful mitigation. |
| SPHINCS+ | Large (e.g., SPHINCS+-Shake256-128s: 32 bytes public key, 32 bytes secret key) | 7680 - 16384 bytes (depending on parameter set) | Estimated equivalent to AES-128/192/256 | Very High – generally the slowest of the selected algorithms | Stateless signature scheme; highly resistant to side-channel attacks; provides strong security guarantees. | Very large signature sizes; slow signature generation and verification; less practical for bandwidth-constrained environments. |
| Kyber512 | 512 bytes public key, 160 bytes secret key | N/A - Key Encapsulation Mechanism (KEM) | Estimated equivalent to AES-128 | Moderate | Offers a good balance between security and performance for applications requiring lower security levels. | Lower security level compared to Kyber768 and Kyber1024. |
| Dilithium2 | 1360 bytes public key, 1360 bytes secret key | 13952 bytes | Estimated equivalent to AES-128 | Moderate | Provides a lower security option within the Dilithium family. | Larger signature size than some other schemes. |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.
Implementing PQC: A Phased Approach to Transition
Migrating to PQC isn’t a simple matter of swapping out algorithms. It’s a complex, long-term undertaking that requires careful planning and execution. A phased approach minimizes disruption. The NIST Cybersecurity Framework 2.0 provides a solid foundation for this transition, emphasizing the importance of identifying, protecting, detecting, responding, and recovering from cyber threats.
A common strategy is to adopt a hybrid approach, combining classical and post-quantum algorithms. This allows organizations to maintain compatibility with existing systems while gradually introducing PQC. For example, you might use both ECC and Kyber to encrypt data, ensuring that it remains secure even if ECC is broken. This provides a safety net during the transition period.
Cryptographic agility is another critical component. This refers to the ability to easily switch between different cryptographic algorithms without requiring major changes to your infrastructure. This is important because the field of PQC is still evolving, and new algorithms may emerge that offer better performance or security.
Organizations should begin by inventorying their cryptographic assets – identifying all systems and applications that rely on encryption. Then, they can prioritize the most critical systems for PQC migration. This is a multi-year project, and it requires ongoing investment and expertise. It’s not a one-time fix, but a continuous process of adaptation and improvement.
- Inventory cryptographic assets.
- Prioritize critical systems.
- Implement hybrid algorithms.
- Ensure cryptographic agility.
- Continuously monitor and update.
Quantum Key Distribution (QKD): A Different Kind of Security
While PQC focuses on developing new algorithms, Quantum Key Distribution (QKD) takes a fundamentally different approach. Instead of relying on mathematical complexity, QKD uses the laws of quantum mechanics to securely distribute encryption keys. It’s based on the principles of superposition and entanglement – concepts that are inherently unpredictable and tamper-evident.
In a QKD system, two parties exchange photons (particles of light) to establish a shared secret key. Any attempt to eavesdrop on the communication will inevitably disturb the quantum state of the photons, alerting the parties to the presence of an attacker. This provides a theoretically unbreakable level of security.
However, QKD isn’t a panacea. It’s expensive and complex to implement, requiring specialized hardware and infrastructure. It also has distance limitations, as photons can be lost or distorted over long distances. Current QKD systems typically require trusted nodes to relay the key over long distances, which introduces potential vulnerabilities.
Despite these limitations, QKD is gaining traction in certain niche applications, such as securing critical infrastructure and protecting highly sensitive data. It’s often seen as a complementary technology to PQC, providing an additional layer of security.
Hardware Security Modules (HSMs) and PQC
Hardware Security Modules (HSMs) are dedicated hardware devices designed to securely store and manage cryptographic keys. They’re already a crucial part of many organizations’ security infrastructure, protecting sensitive data and enabling secure transactions. As we transition to PQC, HSMs will play an even more important role.
HSMs need to support the new PQC algorithms to enable organizations to use them effectively. This requires firmware updates and potentially hardware upgrades. The challenge lies in the fact that HSMs have long lifecycles, and updating them can be a complex and time-consuming process.
Vendors are actively working to add support for PQC algorithms to their HSMs. However, the pace of adoption varies, and it’s important to choose an HSM vendor that is committed to supporting the latest PQC standards. Some HSMs may also support cryptographic agility, allowing you to easily switch between different algorithms as needed.
Trusted Platform Modules (TPMs), commonly found in laptops and servers, also have a role to play in PQC. They can be used to securely store PQC keys and perform cryptographic operations. However, TPMs typically have limited processing power and storage capacity compared to HSMs.
Staying Informed: Resources and Future Trends
The field of PQC is rapidly evolving, so it’s essential to stay informed about the latest developments. The NIST Post-Quantum Cryptography website (https://csrc.nist.gov/projects/post-quantum-cryptography) is a valuable resource for information about the standardization process and the selected algorithms.
The Cybersecurity and Infrastructure Security Agency (CISA) also provides guidance on PQC implementation (https://www.cisa.gov/topics/cybersecurity-best-practices). Staying up to date with their recommendations is essential for organizations seeking to proactively address the quantum threat.
Emerging trends in PQC include continued research into lattice-based cryptography, code-based cryptography, and multivariate cryptography. Researchers are also exploring new approaches to key exchange and digital signatures. The NIST process isn't a finish line, but a starting point for ongoing innovation.
Quantum computers also have the potential to impact other areas of cybersecurity, such as intrusion detection and malware analysis. Quantum machine learning algorithms could be used to identify and respond to threats more effectively. However, this is still a nascent field, and much more research is needed.
Content is being updated. Check back soon.
The Role of Standards and Regulations in PQC Adoption
Widespread adoption of PQC will require clear standards and regulations. Organizations like NIST and CISA are playing a key role in developing these standards, providing guidance on algorithm selection, implementation, and best practices. The NIST Cybersecurity Framework 2.0 will likely incorporate PQC requirements in future revisions.
We can anticipate that government regulations will eventually mandate the use of PQC in certain sectors, particularly those that handle sensitive data, such as finance, healthcare, and defense. Failing to comply with these regulations could result in significant penalties and reputational damage.
International collaboration is also crucial. Different countries and regions are pursuing their own PQC initiatives, and it’s important to ensure interoperability and avoid fragmentation. Organizations like the European Union Agency for Cybersecurity (ENISA) are working to harmonize PQC standards across Europe.
The legal implications of transitioning to PQC are also worth considering. Organizations may need to update their contracts and agreements to reflect the use of new cryptographic algorithms. They should also be prepared to address potential liability issues related to data breaches that occur during the transition period. Proactive planning and adherence to emerging standards will be essential for navigating this complex landscape.
Ethical Hacking Roadmap
— Cybersecurity by Cyberkid (@Anastasis_King) April 12, 2026
Starting from zero? This roadmap shows the learning path from beginner fundamentals to CEH / OSCP preparation.
Focus on networking, Linux, security tools, methodology, and hands-on labs before moving into advanced certifications.
Comment ROADMAP if… pic.twitter.com/5snT8e96KA


No comments yet. Be the first to share your thoughts!