The quantum timeline
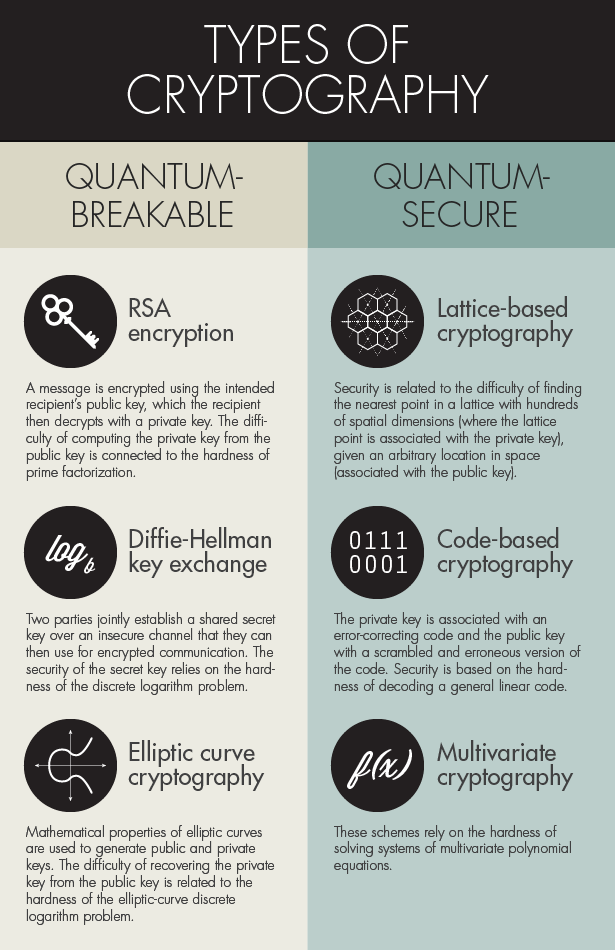
The threat of quantum computers breaking modern encryption isn’t science fiction, but it’s also not an immediate catastrophe. The core issue stems from Shor’s algorithm, developed in 1994, which demonstrates the potential for a quantum computer to efficiently factor large numbers and compute discrete logarithms – the mathematical foundations of widely used public-key cryptography like RSA and Elliptic Curve Cryptography (ECC). This means that much of the secure communication we rely on today, from online banking to secure websites, could become vulnerable.
Estimating when quantum computers will pose a real threat is difficult. Experts disagree, and progress in quantum hardware is unpredictable. Most estimates center around the 2030-2040 timeframe for building a cryptographically relevant quantum computer – one capable of breaking current encryption standards. However, the "harvest now, decrypt later" attack strategy adds urgency. Attackers are already intercepting encrypted data with the intention of decrypting it once quantum computers become powerful enough.
Currently, quantum computers are still in their nascent stages. They suffer from issues with qubit stability, coherence, and scalability. IBM, Google, and other companies are making progress, but building a fault-tolerant quantum computer with enough qubits to run Shor’s algorithm remains a significant engineering challenge. The number of stable, reliable qubits needed is estimated to be in the thousands, and we’re still operating in the dozens and low hundreds.
These timelines are guesses. A single breakthrough in error correction could move the date up by years, while hardware scaling issues might push it back. Preparing now is about managing that uncertainty rather than waiting for a deadline that might move.
New algorithms for a post-quantum world
Post-Quantum Cryptography (PQC) refers to cryptographic algorithms that are believed to be secure against attacks by both classical and quantum computers. The National Institute of Standards and Technology (NIST) has been leading a multi-year effort to standardize new PQC algorithms. In 2022, NIST announced the first set of algorithms selected for standardization, marking a significant milestone in the transition to quantum-safe cryptography.
The selected algorithms fall into several categories, each based on different mathematical problems. CRYSTALS-Kyber and CRYSTALS-Dilithium are lattice-based algorithms, considered strong candidates due to their performance and security. Falcon is another lattice-based scheme offering advantages in signature size. SPHINCS+ is a stateful hash-based signature scheme, providing a different security foundation.
Lattice-based cryptography relies on the difficulty of solving problems involving lattices – geometric structures in high-dimensional space. Code-based cryptography, while not initially selected for primary standardization, is based on the difficulty of decoding general linear codes. Multivariate cryptography uses systems of polynomial equations, and hash-based signatures rely on the security of cryptographic hash functions. Each approach has its own strengths and weaknesses.
It’s crucial to understand that PQC algorithms aren’t meant to add to existing security measures, but to replace them. RSA and ECC will eventually become vulnerable, and these new algorithms are designed to take their place. The transition won’t be seamless, and careful planning is needed to ensure compatibility and maintain security throughout the process. There's ongoing research into the performance and side-channel vulnerabilities of these algorithms, so the standardization process is iterative.
- CRYSTALS-Kyber handles key-encapsulation to establish shared secrets.
- CRYSTALS-Dilithium: Digital signature algorithm.
- Falcon: Digital signature algorithm – prioritizes smaller signature sizes.
- SPHINCS+: Digital signature algorithm – particularly resilient, but less efficient.
NIST Post-Quantum Cryptography (PQC) Finalist Comparison - 2026
| Algorithm Name | Category | Key Size (approximate) | Signature Size (approximate) | Security Considerations |
|---|---|---|---|---|
| CRYSTALS-Kyber | Lattice-based Key Encapsulation Mechanism (KEM) | 768 bytes (Kyber512) | 768 bytes | Generally considered to have a good security margin, but ongoing analysis continues to refine understanding of lattice structure vulnerabilities. |
| CRYSTALS-Dilithium | Lattice-based Digital Signature | 2528 bytes (Dilithium2) | 2048 bytes | Offers a relatively small signature size. Security relies on the hardness of lattice problems, and research continues on potential attacks. |
| Falcon | Lattice-based Digital Signature | 1280 bytes (Falcon-512) | 690 bytes | Known for its compact signature sizes. Security is based on the Shortest Integer Solution (SIS) problem on lattices. Ongoing research focuses on side-channel resistance. |
| SPHINCS+ | Hash-based Digital Signature | Variable, depending on security level (e.g., 32-64 bytes for moderate security) | Variable, larger than lattice-based signatures (e.g., 7.6-15.2 KB) | Provides strong security based on the assumed security of hash functions. Larger signature sizes are a primary drawback. Stateless nature simplifies key management. |
| Rainbow | Multivariate Quadratic (MQ) Digital Signature | Approximately 1 KB (RainbowV-I) | Approximately 256 bytes | Security is based on the difficulty of solving systems of multivariate polynomial equations. Concerns exist about potential structural attacks and the need for large key sizes. |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.
Why hybrid encryption is the safest bet
A practical approach to mitigating the quantum threat is to adopt hybrid cryptography, which combines classical cryptographic algorithms with PQC algorithms. This involves using both RSA or ECC and a PQC algorithm in the same cryptographic operation. The idea is that even if one algorithm is broken, the other will still provide security.
Hybrid cryptography offers several benefits. It provides backwards compatibility, allowing systems to continue functioning even if PQC implementations have issues. It also reduces the risk associated with relying solely on new, unproven algorithms. If a weakness is discovered in a PQC algorithm, the classical algorithm still provides a layer of defense.
Several hybrid schemes and libraries are emerging. OpenSSL, a widely used cryptography library, has begun incorporating PQC algorithms, enabling hybrid key exchange. However, managing multiple cryptographic systems simultaneously presents challenges. It requires careful configuration, testing, and monitoring to ensure that the hybrid scheme is implemented correctly and securely.
The transition to PQC won’t happen overnight. Hybrid approaches provide a sensible pathway for organizations to begin preparing for the quantum era without disrupting existing systems. The key is to start experimenting and building expertise now.
- Backwards Compatibility: Maintains functionality with existing systems.
- Reduced Risk: Provides a fallback if a PQC algorithm is compromised.
- Gradual Transition: Allows organizations to adopt PQC at their own pace.
Quantum Key Distribution (QKD): A Different Path
Quantum Key Distribution (QKD) represents a fundamentally different approach to cryptography. Instead of relying on mathematical algorithms, QKD leverages the laws of quantum physics to securely distribute encryption keys. It works by encoding cryptographic keys onto photons (particles of light) and transmitting them over a quantum channel.
The security of QKD is based on the principle that any attempt to intercept or measure the photons will disturb their quantum state, alerting the sender and receiver to the presence of an eavesdropper. This makes it theoretically impossible for an attacker to intercept the key without being detected. This contrasts with PQC, which relies on the computational difficulty of certain mathematical problems.
However, QKD has significant limitations. Its range is limited by signal attenuation and noise, requiring trusted nodes to extend the distance. It’s also expensive to deploy and maintain, requiring specialized hardware and infrastructure. QKD is not a software upgrade; it’s a physical layer security solution.
QKD isn’t a universal solution for all organizations. It’s best suited for situations where the highest levels of security are required and the cost and complexity can be justified – such as securing government communications or financial transactions. It's also valuable where long-term key secrecy is paramount.
Securing AI in a Quantum World
AI systems have their own quantum vulnerabilities. If an attacker uses a quantum computer to crack the encryption on training sets, they can poison the data or reverse-engineer proprietary model parameters. This turns a data breach into a permanent compromise of the model's logic.
The implications are significant. If an attacker can manipulate the training data, they could cause the model to make incorrect predictions or exhibit biased behavior. Compromising model parameters could allow an attacker to control the model’s output. Extracting sensitive information from a trained model could reveal confidential data used during the training process.
Protecting AI systems requires a multi-faceted approach. This includes using quantum-safe cryptography to secure the data used for training and inference, as well as developing quantum-resistant machine learning algorithms. Techniques like homomorphic encryption – which allows computations to be performed on encrypted data – and federated learning – which allows models to be trained on decentralized data without sharing the data itself – can also help mitigate the risk.
The convergence of AI and quantum computing presents both opportunities and challenges. While quantum computers pose a threat to AI systems, they also have the potential to accelerate AI research and development. Ensuring the security of AI in a quantum world will require a collaborative effort between cryptographers, machine learning experts, and security professionals.
Certificate Authorities and Quantum Resistance
Certificate Authorities (CAs) play a critical role in establishing trust on the internet. They issue and manage digital certificates, which are used to verify the identity of websites and other online entities. The transition to quantum-safe cryptography will require CAs to adapt their infrastructure and processes.
Keyfactor.com emphasizes the evolving nature of digital trust management in the quantum era. CAs will need to issue and manage PQC-based certificates, which will require new algorithms, key generation techniques, and certificate formats. The Public Key Infrastructure (PKI) – the system that underlies digital certificates – will need to be updated to support PQC.
Updating the PKI is a complex undertaking. It requires coordinating changes across a vast network of CAs, browsers, operating systems, and other software. There are also challenges related to certificate revocation and key compromise. Ensuring interoperability between different PQC implementations is crucial.
The implications for website security (HTTPS) are significant. HTTPS relies on digital certificates to encrypt communication between web browsers and web servers. Once quantum computers become a threat, current HTTPS certificates will become vulnerable. The transition to PQC-based certificates is essential to maintain the security of online transactions and data.
What you should do in 2026
The time to prepare for the quantum threat is now, even if widespread deployment of PQC is still some years away. For tech experts, the next 12-18 months should focus on awareness, assessment, and planning. This isn’t about immediately replacing all existing cryptography, but about laying the groundwork for a smooth transition.
First, stay informed about the latest developments in PQC. Follow NIST’s standardization efforts and keep abreast of new research and best practices. Second, begin experimenting with PQC libraries and tools. Familiarize yourself with the new algorithms and their performance characteristics. Third, assess your organization’s risk. Identify which systems and data are most vulnerable to quantum attacks.
Fourth, advocate for PQC adoption within your organization. Educate stakeholders about the threat and the importance of preparing for it. Fifth, contribute to the community. Share your knowledge and experience with others. Participate in open-source projects and contribute to the development of PQC tools and libraries.
Finally, start inventorying your cryptographic assets. Understand where cryptography is used in your systems and applications. This is a crucial first step toward identifying and mitigating vulnerabilities.
- Stay informed about NIST standards.
- Test PQC libraries like liboqs in a sandbox to see how they hit your CPU.
- Assess your organization’s risk.
- Advocate for PQC adoption.
- Inventory cryptographic assets.


No comments yet. Be the first to share your thoughts!