Moving past the castle-and-moat model
For decades, network security operated on a 'castle-and-moat' model. Strong defenses guarded the network perimeter, assuming everything inside was trustworthy. This approach is demonstrably failing. Modern threats – sophisticated malware, insider threats, and compromised credentials – routinely bypass perimeter defenses, and the increasing move to remote work and cloud services has effectively dissolved the traditional perimeter altogether.
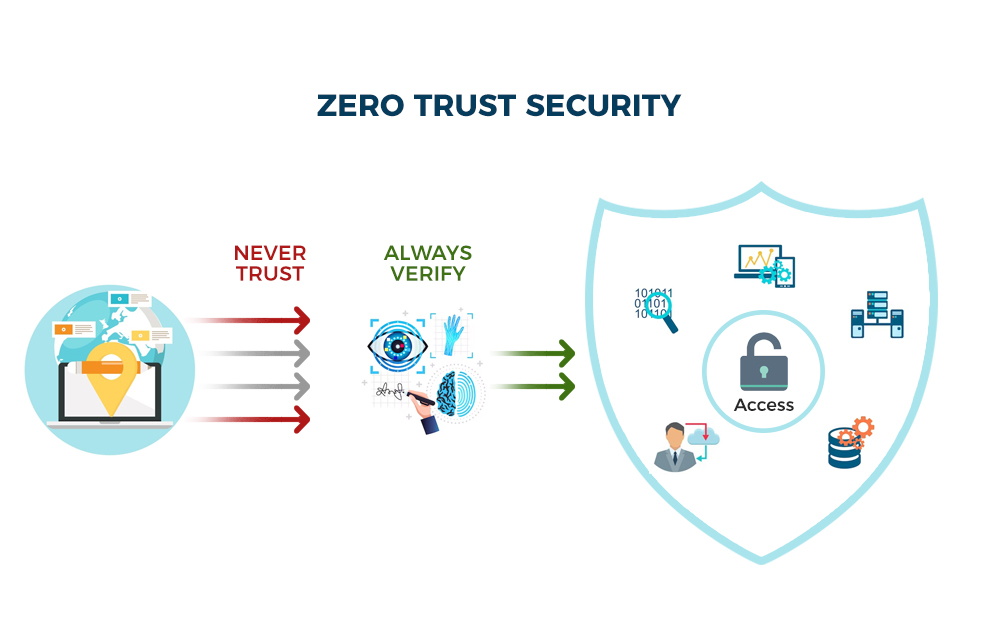
The fundamental problem is trust. Traditional models implicitly trust users and devices once they’re inside the network. Zero Trust flips this on its head. The core principle is simple: 'never trust, always verify'. Every user, device, and application – whether inside or outside the network – must be authenticated and authorized before being granted access to resources. This isn’t about building a better wall; it’s about removing the idea of a trusted internal network entirely.
Zero Trust isn’t a single product you can purchase and install. It’s a security philosophy, a fundamental shift in how we think about network access. It demands a holistic approach, encompassing technology, processes, and people. While vendors offer tools to enable Zero Trust, successful implementation requires careful planning and a deep understanding of your organization’s specific needs and risk profile. It's a journey, not a destination.
The seven pillars of zero trust
The National Institute of Standards and Technology (NIST) has outlined seven key pillars of a Zero Trust Architecture in Special Publication 800-207. These pillars aren’t isolated concepts; they work together to create a robust security posture. Understanding these pillars is essential for effective Zero Trust implementation.
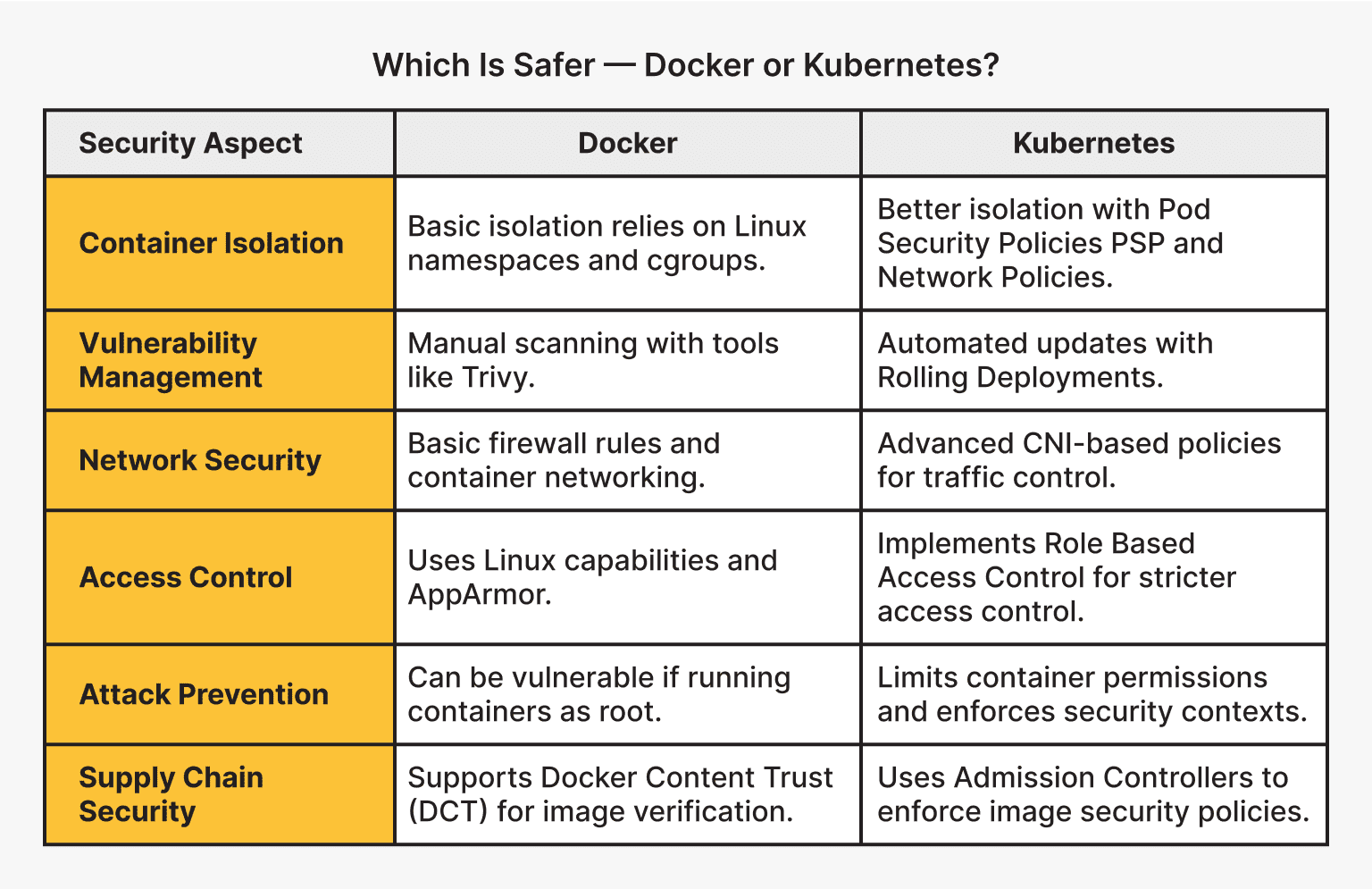
Data Security focuses on classifying data, understanding its sensitivity, and applying appropriate security controls. This includes encryption, access controls, and data loss prevention (DLP) measures. Command Plane Security is about protecting the infrastructure that manages and controls the network, ensuring only authorized personnel can make changes. Programming Interface Security is critical as more systems rely on APIs for communication – securing these interfaces prevents unauthorized access and manipulation.
Infrastructure Security deals with securing the underlying network infrastructure – servers, routers, switches, and firewalls. Workload Security focuses on protecting individual applications and workloads, often through microsegmentation and containerization. Visibility and Analytics are about collecting and analyzing data to detect and respond to threats. This relies heavily on logging, monitoring, and threat intelligence. Finally, Automation is crucial for scaling Zero Trust across a complex environment, automating tasks like authentication, authorization, and incident response.
These pillars are interconnected. For example, strong identity verification (a component of Command Plane Security) is essential for enforcing least privilege access (Data Security). Continuous monitoring (Visibility and Analytics) helps identify vulnerabilities and inform security policies (Infrastructure Security). A successful Zero Trust architecture requires careful consideration of how these pillars interact and reinforce each other.
- Remove entire list.
- Command Plane Security
- Programming Interface Security
- Infrastructure Security
- Workload Security
- Visibility and Analytics
- Automation
Identity is the new perimeter
Zero Trust fundamentally relies on verifying who is requesting access. This makes Identity and Access Management (IAM) the cornerstone of any Zero Trust architecture. Without strong identity verification, all other security measures are significantly weakened.
Multi-Factor Authentication (MFA) is non-negotiable. Requiring users to provide multiple forms of identification – something they know (password), something they have (phone), and something they are (biometrics) – dramatically reduces the risk of compromised credentials. Privileged Access Management (PAM) is equally important, controlling and monitoring access to sensitive systems and data. The principle of least privilege – granting users only the access they need to perform their job – minimizes the potential damage from a breach.
Relying solely on passwords is a significant vulnerability. Passwordless authentication methods, such as biometrics, security keys, and certificate-based authentication, offer a more secure and user-friendly alternative. IAM solutions must integrate with other Zero Trust components, like microsegmentation and continuous monitoring, to provide a comprehensive security posture.
- Implement Multi-Factor Authentication (MFA) for all users.
- Deploy Privileged Access Management (PAM) to control access to sensitive systems.
- Enforce the principle of least privilege.
- Consider passwordless authentication methods.
Microsegmentation: Limiting the Blast Radius
Microsegmentation divides a network into small, isolated segments, controlling traffic flow between them. Unlike traditional network segmentation, which often creates broad zones, microsegmentation creates granular policies based on application, workload, or user identity. This significantly reduces the attack surface and limits the blast radius of a breach.
Traditional segmentation might separate the finance department from the marketing department. Microsegmentation might isolate a specific application within the finance department, allowing communication only with the databases it needs to access. This prevents an attacker who compromises one application from easily moving laterally across the network. It’s about containing damage, not just preventing initial entry.
Microsegmentation can be implemented in various environments. In the cloud, security groups and network access control lists (ACLs) can be used to create microsegments. On-premise, software-defined networking (SDN) and network virtualization technologies enable granular segmentation. Hybrid environments require a consistent approach across both on-premise and cloud infrastructure. The complexity increases with scale, which is why automation is so important.
Continuous Monitoring and Analytics
Zero Trust isn’t a 'set it and forget it' approach. Continuous monitoring and analytics are essential for detecting and responding to threats in real-time. Constant vigilance is required to identify anomalies and suspicious activity that could indicate a breach.
Security Information and Event Management (SIEM) systems collect and analyze logs from various sources, providing a centralized view of security events. User and Entity Behavior Analytics (UEBA) goes a step further, using machine learning to establish baseline behavior patterns and detect deviations that could indicate malicious activity. These tools aren’t silver bullets; they require careful configuration and ongoing tuning to minimize false positives.
When picking a SIEM or UEBA tool, prioritize those that can correlate data from different sources automatically. You need a system that spots a weird login and immediately checks it against recent file access logs. Focus on tools that offer automated response rather than just sending another alert to an overflowing inbox.
Practical tips from the NSA guidance
The National Security Agency (NSA) has released guidance on Zero Trust implementation, emphasizing automation, data-centric security, and a layered defense. Their recommendations align closely with the NIST framework but offer a more prescriptive approach, reflecting the agency’s focus on national security.
The NSA stresses the importance of automating security controls as much as possible, reducing the reliance on manual processes. They advocate for a data-centric security model, protecting data itself rather than focusing solely on network perimeters. A layered defense – combining multiple security controls – is also a key tenet of their guidance. This means implementing multiple layers of authentication, authorization, and monitoring.
The NSA guidance complements the NIST framework by providing practical implementation details. While NIST outlines the 'what' of Zero Trust, the NSA offers insights into the 'how'. Both frameworks recognize the importance of continuous monitoring, strong identity verification, and least privilege access. They aren’t conflicting approaches, but rather different perspectives on achieving the same goal: a more secure network.


No comments yet. Be the first to share your thoughts!