Zero trust basics
Network security used to rely on the 'castle-and-moat' model, trusting anything inside the perimeter. This failed as apps moved to the cloud and teams went remote. Now, the perimeter is effectively gone.
Zero Trust isn't a product you buy; it’s a security framework. It fundamentally shifts the focus from network location to user and device identity. The core idea is never trust, always verify. Every user, every device, every application attempting to access resources must be authenticated, authorized, and continuously validated, regardless of whether they're inside or outside the network. It’s about minimizing implicit trust.
Zero Trust stops lateral movement. In traditional setups, an attacker who gets into one segment can often roam the entire network. Cloud environments don't have a physical edge to defend, so security has to follow the data rather than the wires.
The NIST 800-207 framework
The National Institute of Standards and Technology (NIST) Special Publication 800-207 is the foundational document for Zero Trust architecture. It provides a comprehensive framework for understanding and implementing Zero Trust principles. It’s not a prescriptive checklist, but rather a set of guidelines to help organizations build a more secure network.
The framework is built around seven pillars: Identity, Device, Network, Application Workloads, Data, Visibility & Analytics, and Automation & Orchestration. These pillars aren’t isolated; they're interconnected and work together to create a holistic security posture. Identity is the foundation – verifying who is requesting access. Device security ensures the device itself is trustworthy. Network segmentation limits the blast radius of potential breaches. Application Workloads focuses on securing individual applications. Data security protects sensitive information. Visibility & Analytics provides the insights needed to detect and respond to threats. Finally, Automation & Orchestration streamlines security operations.
A key concept underlying all these pillars is 'least privilege'. This means granting users and devices only the minimum level of access necessary to perform their tasks. It’s not enough to simply authenticate a user; you must also authorize them to access specific resources, and continuously monitor their activity. Each pillar reinforces this principle, creating a layered defense that minimizes the risk of unauthorized access and data breaches.
- Identity: Verifying the user behind the request.
- Device
- Network
- Application Workloads
- Data
- Visibility & Analytics
- Automation & Orchestration
Microsegmentation and lateral movement
Traditional network segmentation divides the network into broad zones, like separating the marketing department from engineering. Microsegmentation takes this concept to a much more granular level, creating isolated segments for individual applications, workloads, or even specific users. This significantly reduces the attack surface and limits the potential impact of a breach.
Unlike traditional segmentation, which often relies on static IP addresses and network rules, microsegmentation dynamically adjusts based on application behavior and user context. If an attacker compromises one segment, they are contained within that segment and cannot easily move laterally to other parts of the network. This is a significant improvement over traditional security models.
Implementing microsegmentation isn’t without its challenges. It can be complex to configure and manage, especially in large, dynamic environments. It requires a deep understanding of application dependencies and network traffic patterns. However, the benefits – reduced blast radius, improved compliance, and enhanced security – often outweigh the complexities. Approaches can include application-based segmentation, workload-based segmentation, or a combination of both.
Identity and Access Management (IAM) in a Zero Trust World
Identity is the cornerstone of Zero Trust. If you can’t reliably verify who a user is, you can’t trust any request for access. This is where Identity and Access Management (IAM) comes into play. IAM encompasses a range of technologies and processes designed to manage digital identities and control access to resources.
Multi-factor authentication (MFA) is the baseline. Using hardware tokens or biometrics alongside passwords makes credential theft much harder. Privileged access management (PAM) adds another layer by restricting who can touch the most sensitive databases.
Zero Trust demands continuous authentication and authorization. It’s not enough to verify a user’s identity once; you must continuously monitor their behavior and re-authenticate them as needed. Identity Governance and Administration (IGA) plays a role here, automating the process of managing user identities and access rights. IAM needs to integrate with other Zero Trust components, such as network segmentation and application security, to provide a comprehensive security posture.
Encryption and data loss prevention
Zero Trust principles extend to data security, focusing on protecting sensitive information regardless of where it resides. Data encryption, both in transit and at rest, is fundamental. Encrypting data makes it unreadable to unauthorized users, even if they gain access to the storage medium.
Data Loss Prevention (DLP) technologies help prevent sensitive data from leaving the organization's control. DLP tools can identify and block the transfer of confidential information via email, USB drives, or cloud storage. Data classification is also crucial – identifying and labeling data based on its sensitivity level allows you to apply appropriate security controls.
Understanding where your data is is the first step towards protecting it. Zero Trust emphasizes data visibility and auditing. You need to know what data you have, where it's located, and who has access to it. Continuous monitoring and logging of data access events are essential for detecting and responding to potential data breaches.
Implementing Zero Trust: A Phased Approach
Implementing Zero Trust isn’t a one-time project; it’s a journey. It requires a phased approach, starting with a thorough assessment of your current security posture and prioritizing the most critical assets. Trying to implement Zero Trust across the entire organization at once is likely to be overwhelming and ineffective.
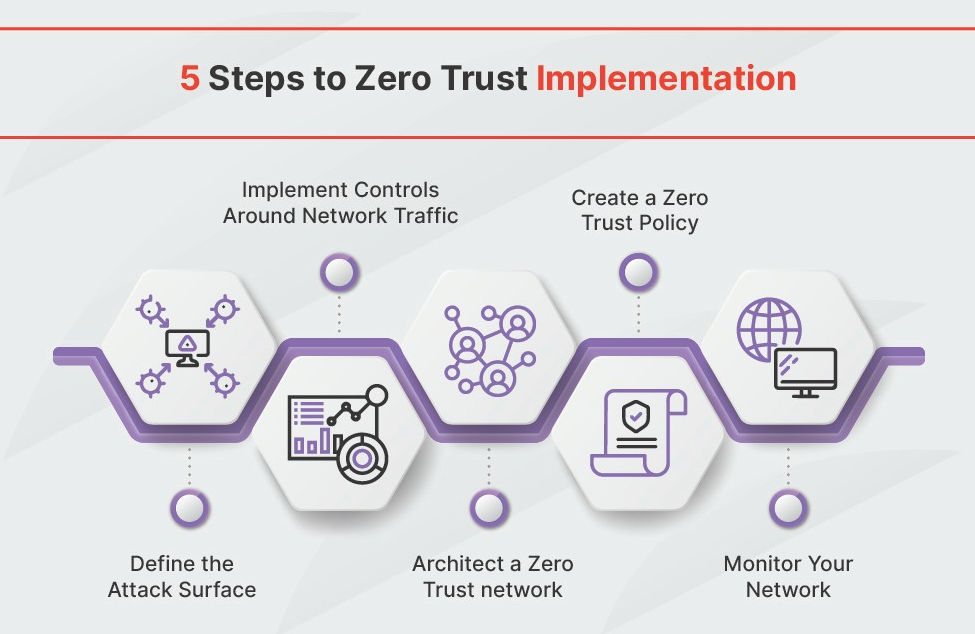
A common approach involves these steps: First, Identify Protect Surface. Determine the critical data, assets, applications, and services that need to be protected. Second, Map Transaction Flows. Understand how data flows through your network and identify potential vulnerabilities. Third, Build a Zero Trust Architecture. Implement the necessary security controls, such as microsegmentation, MFA, and data encryption. Fourth, Create Zero Trust Policies. Define clear policies that govern access to resources. Finally, Monitor and Maintain. Continuously monitor your environment, adapt your policies, and stay ahead of emerging threats.
Starting small and focusing on the most critical assets first is key. For example, you might begin by implementing Zero Trust for remote access to sensitive applications. Automation plays a vital role in Zero Trust implementation, streamlining security operations and reducing the risk of human error. Orchestration tools can automate tasks such as policy enforcement, threat detection, and incident response. It’s about building security into your systems, not bolting it on as an afterthought.
- Identify Protect Surface
- Map Transaction Flows
- Build a Zero Trust Architecture
- Create Zero Trust Policies
- Monitor and Maintain



No comments yet. Be the first to share your thoughts!