What matters most
The biggest trap in Linux disk space cleanup is assuming that every command that frees up space is safe to run blindly. Disk space is a resource, not a puzzle to be solved with sledgehammers. Running the wrong purge command can remove critical system libraries, orphaned configuration files, or even active packages that your desktop environment relies on.
The goal isn't just to reclaim gigabytes; it's to do so without breaking the system you're trying to maintain. This means prioritizing commands that target obvious, disposable data—like old kernel images, package manager caches, and orphaned dependencies—over aggressive sweeps that might touch active configurations.
Community consensus from platforms like Ask Ubuntu and Stack Exchange consistently points to a few safe, high-yield actions. These include cleaning the APT cache, removing orphaned packages, and purging packages that have been uninstalled but left their configuration files behind. These commands are low-risk because they operate on data that is either redundant or already marked for removal.
However, caution is still required. Always verify what a command will delete before hitting enter. For instance, while apt autoremove is generally safe, it might remove packages that were manually installed as dependencies for other tools. The safest approach is to review the list of packages that will be removed before confirming the action.
Details to compare
Before running cleanup commands, it helps to understand what each tool actually does and where the risks lie. Not all space-reclaiming methods are created equal, and some carry a higher chance of breaking system updates or removing user data by mistake. Evaluating these factors lets you choose the right command for your specific situation.
The primary distinction is between safe, automated maintenance and manual, targeted purging. Automated tools like apt autoremove or journalctl --vacuum-time are generally low-risk because they follow established system policies. Manual commands like rm -rf or dpkg --purge require you to verify every package or file, increasing the chance of human error.
Another factor is reversibility. Can you undo the action if something goes wrong? Commands that delete logs or caches are often reversible by simply letting the system regenerate them. Commands that remove installed packages or configuration files are permanent unless you have a backup. Always check if a command has a --dry-run or --simulate flag before executing it.
Finally, consider the scope of impact. Some commands affect only your user directory, while others require sudo and touch system-wide directories. System-wide commands can free up more space but may disrupt services if critical files are removed. Start with user-level commands to gauge how much space you can safely reclaim.
| Command | Risk Level | Reversible | Scope |
|---|---|---|---|
| apt autoremove | Low | Yes (apt install) | System-wide |
| journalctl --vacuum-size | Low | No | System-wide |
| rm -rf ~/.cache | Medium | Yes (rebuild) | User-level |
| dpkg --purge | High | No | System-wide |
Community insights
The Linux community often emphasizes caution with manual purging. Many users report that apt autoremove is the safest first step, as it only removes dependencies that are no longer needed. However, some users have encountered issues with dpkg commands removing essential packages if not filtered correctly.
"Switch to a virtual terminal (TTY) and back with Ctrl+Alt+F1. Once you have freed up enough disk space you can switch back."— Linux StackExchange
This quote highlights a critical safety tip: if your system becomes too full to boot properly, you can often recover by switching to a TTY and manually deleting large files or logs. This is a last-resort method, but it can save a system that would otherwise require a full reinstall.
How to decide what to clean
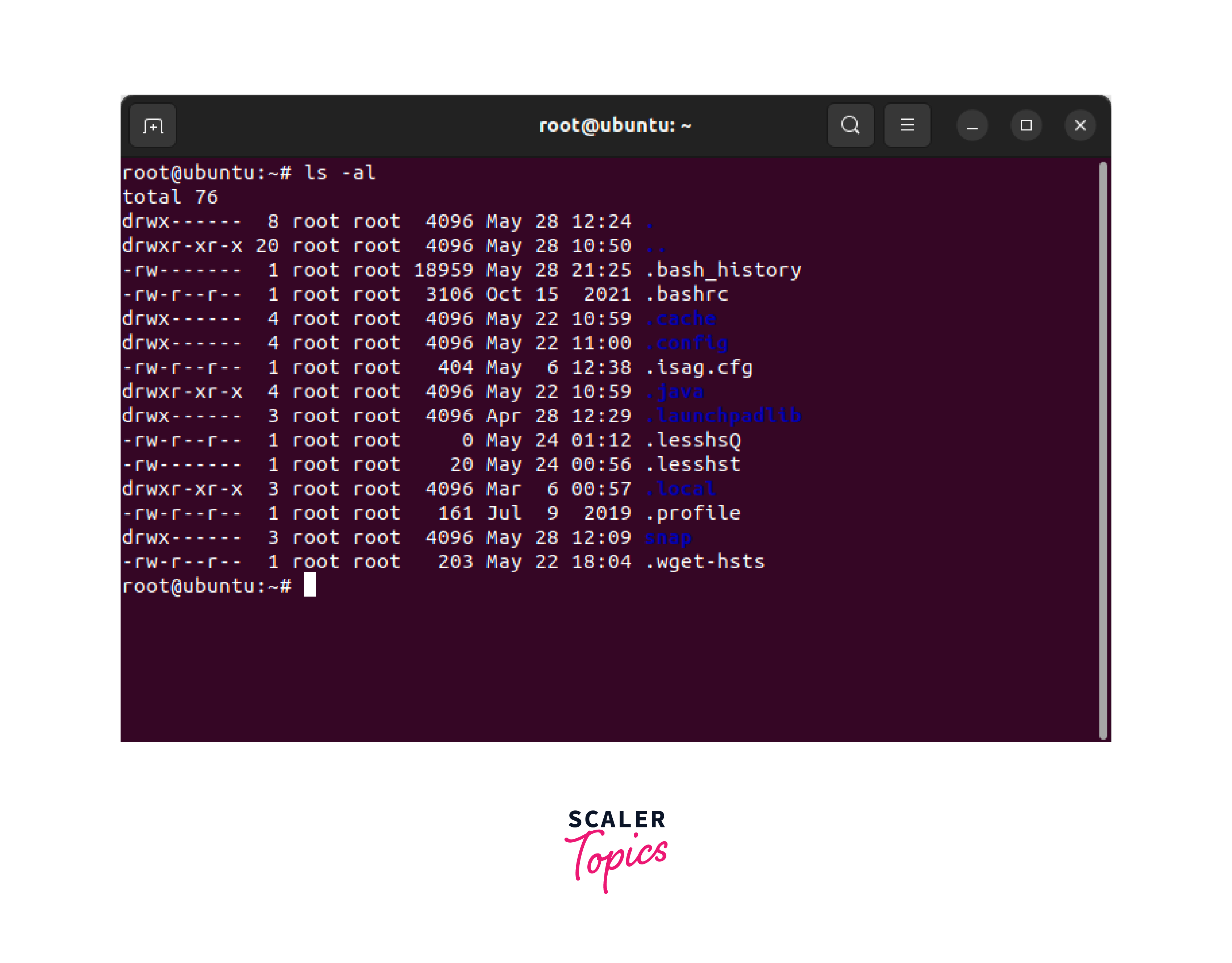
Before running cleanup commands, you need a clear picture of what is actually taking up space. Blindly deleting files can break your system, so start by identifying the largest consumers. The df -h command shows overall partition usage, but it doesn't tell you which folders are the culprits. For that, use du -sh /* to scan top-level directories, or run ncdu for an interactive, navigable view of disk usage. This step is critical because it prevents you from deleting small files that don't matter or missing large caches that do.
Once you know where the space is going, categorize the files into safe and risky groups. Safe targets usually include package manager caches, old kernel images, and temporary files. Risky targets include user documents, application data, and system libraries. A good rule of thumb is to only delete files you recognize as transient or generated data. If you are unsure about a file's purpose, leave it alone. The goal is to reclaim space without breaking the tools you rely on daily.
Prioritize your cleanup based on the source of the bloat. On Debian-based systems, the package manager cache (/var/cache/apt) is often the easiest win. On other distributions, look for /var/cache/pacman or /var/cache/yum. Docker users should check for unused images and containers, which can consume gigabytes without you realizing it. Start with these low-risk, high-reward areas before moving to more complex manual deletions.
Finally, verify your changes. After running your chosen cleanup commands, check your disk usage again with df -h. If the space hasn't freed up significantly, you may need to dig deeper into specific applications or logs. Remember that some files are held open by running processes; if df shows usage but du doesn't match, restart the affected services or reboot the system to release those locks.
What to Avoid
Cleaning a Linux system is straightforward until you start guessing. Many guides suggest running aggressive cleanup scripts or blindly deleting files from /tmp and /var. This approach is risky because it often removes active logs, package caches your system relies on, or even critical configuration files. Instead of relying on unverified one-liners, stick to commands that are documented and reversible.
Dangerous Commands and Misleading Scripts
Avoid any command that suggests using rm -rf on system directories like /var/cache or /usr without explicit package manager flags. A common mistake is deleting old kernel images manually instead of using your distribution’s package manager (like apt autoremove or dnf system-upgrade). Manual deletion leaves orphaned dependencies and can break package integrity checks. Similarly, scripts that purge all user data in /tmp can disrupt running services that rely on temporary sockets or state files.
The Virtual Terminal Trap
Some advice suggests switching to a TTY (Ctrl+Alt+F1) to free up space by killing graphical processes. While this works in emergencies, it is not a standard cleanup method. It leaves your system in a degraded state and doesn’t address the root cause of disk usage. Use package managers and targeted log rotation instead. If you must use TTY, remember to switch back carefully once space is freed.
Community-Verified Safe Practices
The most reliable advice from Linux communities focuses on package management. Use dpkg -l | grep ^rc to find and purge residual config files left by uninstalled packages. For Docker users, docker system prune is safe if you’re sure you don’t need stopped containers. These methods are specific, documented, and safe to run on production systems.
Common questions about Linux disk cleanup
Users often worry about accidentally deleting essential files or breaking system stability. The commands below are generally safe when used correctly, but understanding the scope of each action helps prevent unintended data loss.
Is it safe to delete files in /tmp?
Yes. The /tmp directory is reserved for temporary files created by applications and the system. These files are typically older than 10 days and are safe to remove. However, if a program is currently using a file in /tmp, the system will not delete it. To clear old temporary files safely, use sudo find /tmp -type f -atime +10 -delete.
Can I run apt-get autoremove without breaking packages?
This command is safe and recommended for Debian-based systems like Ubuntu. It removes packages that were automatically installed as dependencies but are no longer required by any manually installed software. To preview what will be removed without deleting anything, run sudo apt-get autoremove --dry-run first.
How do I clean system logs without stopping services?
You can safely vacuum journal logs using sudo journalctl --vacuum-size=500M. This command keeps only the last 500MB of logs, deleting older entries. It does not stop or restart any services; it simply removes archived log files from disk. Always verify the current log size with journalctl --disk-usage before vacuuming.
Why doesn't freed space show up immediately?
Sometimes, running cleanup commands doesn't immediately increase your available disk space. This is often due to cached data still held in memory or open file handles. Running sync flushes pending writes to disk, and a reboot clears memory caches and releases locked files. If space is still full, check for deleted files still held open by processes using lsof | grep deleted.


No comments yet. Be the first to share your thoughts!