Unlocking the Power of Linux in Cybersecurity: A Starter's Guide 🚀
In a world where our digital footprints are as real as our physical ones, mastering cybersecurity is no longer a luxury—it's a necessity. The stakes? Everything from your personal data to the integrity of global infrastructures. So, where does Linux enter this narrative? Why is Linux important to learn for cyber security, you ask?
Imagine Linux as your digital fortress, a stronghold in the vast landscape of the internet. With its robust architecture and an arsenal of cybersecurity tools, Linux offers a formidable defense against the lurking threats in the digital world. It's not just an operating system; it's a cyber knight safeguarding your data.
As we delve deeper into this comprehensive Linux cybersecurity guide, you'll discover why mastering cybersecurity with Linux isn't just an option—it's the smart choice for anyone serious about digital security. So, are you ready to become a cyber warrior with the best Linux distros for cybersecurity?
Let's dive into the dynamic world of Linux, a powerhouse of flexibility and customization that stands tall among other operating systems. But why is Linux important to learn for cyber security, you may wonder? Well, it's simple. Linux offers an open-source platform, allowing you to peek under the hood, understand the mechanics, and modify as per your needs. This transparency is a boon for those aiming to master cybersecurity with Linux.
Linux distros, each with their unique flavors, offer an array of cybersecurity tools. They can be your perfect allies in the digital battlefield, helping you fortify your defenses and counteract cyber threats. This comprehensive Linux cybersecurity guide aims to take you on a journey, unveiling the secrets of mastering Linux security and hardening.
So, are you ready to wield the power of the best Linux distros for cybersecurity? Let's begin this thrilling expedition!

Why Linux Holds the Key to Cybersecurity 🔐
Imagine a fortress, impenetrable and robust, standing tall amidst the relentless waves of cyber threats. This fortress is Linux, your ultimate defense in the digital world. Why, you ask? Well, Linux, unlike its counterparts, is open-source. This means that countless eyes scrutinize its code, making it less likely for vulnerabilities to go unnoticed. It's like having a team of dedicated guardians constantly on the lookout.
But that's not all. Linux provides you with unparalleled control, allowing you to tweak and harden your system to your heart's content. You're not just a user; you're the master of your digital realm. With Linux, you're not just reacting to threats; you're proactively fortifying your defenses. It's no wonder why mastering cybersecurity with Linux is a sought-after skill in today's digital age.
So, ready to embrace the power of Linux for cyber security? Ready to turn your system into a digital fortress? Let's dive into the world of Linux cybersecurity tools and discover the best Linux distros for cybersecurity.
To better understand the scope of cybersecurity in Linux, let's take a look at this informative video by Simplilearn.
Now that we've explored the scope of cybersecurity within the Linux operating system, let's move on to discuss some popular Linux distros known for their security features.
Top Linux Distros: Your Cybersecurity Heroes 🦸♂️
Top Linux Distros for Cybersecurity
- Kali Linux - Known as the 'Swiss Army knife' for cybersecurity professionals, Kali Linux is a distro packed with hundreds of penetration testing tools.

- Parrot Security OS - This distro is designed for penetration testing, vulnerability assessment, computer forensics, and anonymous web browsing.
- BackBox - A Ubuntu-based distro, BackBox offers a minimal yet powerful environment for ethical hacking and security assessment.
- BlackArch Linux - With over 2000+ ethical hacking tools, BlackArch Linux is a comprehensive solution for researchers and cybersecurity professionals.

- Tails - Tails is a privacy-focused Linux distro that routes all internet traffic through the Tor network to ensure user anonymity.

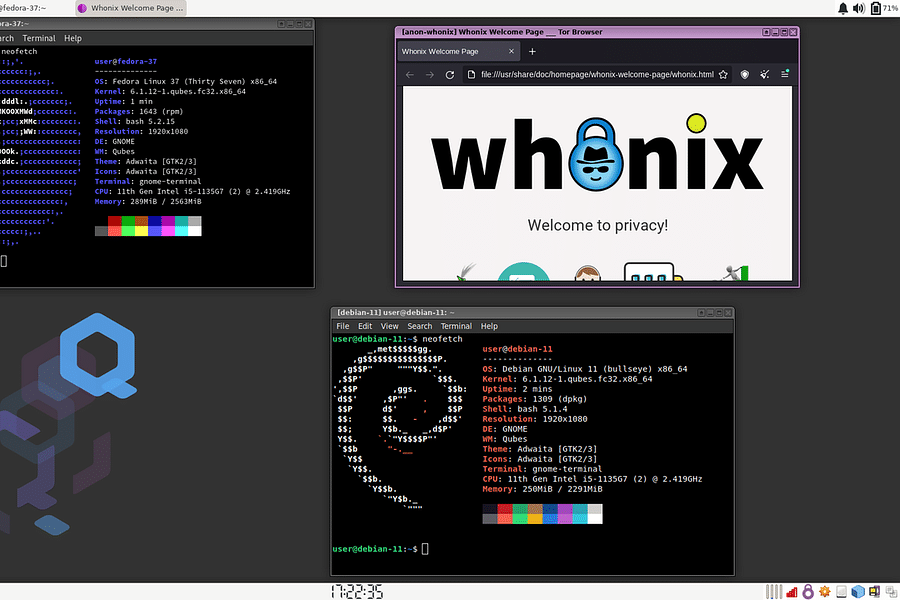
- Qubes OS - Known for its 'security by isolation' approach, Qubes OS uses virtualization to create secure compartments for different tasks.
Supercharge Your Cybersecurity Skills with Linux Distros 💪
Imagine a digital fortress, impregnable and robust. That's what you're building when you're mastering cybersecurity with Linux. So, why is Linux important to learn for cyber security, you ask? Well, with its inherent flexibility and a vast array of powerful distros tailored for cybersecurity, Linux is your secret weapon in this ever-evolving digital battlefield.
Among the best Linux distros for cybersecurity are Kali Linux, Parrot Security OS, and BackBox. Each one is a unique arsenal of pre-installed and customizable security tools. But it's not just about having these tools; it's about knowing how to wield them effectively. That's where this comprehensive Linux cybersecurity guide comes in handy.
But remember, a fortress is only as strong as its weakest point. Linux cybersecurity tools are your bricks and mortar, but understanding and vigilance are the skilled masons. Ready to start building?
Now that we've discussed the importance of Linux distros in cybersecurity, let's dive into setting up a secure environment on a Linux distro.
Learn more about Setting Up a Secure Linux Environment: A Step-by-Step Guide ✅ or discover other Guide Techy guides.
By following these steps, you've created a secure foundation for your Linux environment. Now, let's look at some sample scripts showing security implementation on Linux.
Setting Up a Basic Secure Environment on Linux
In this section, we will demonstrate how to set up a basic secure environment on a Linux distro using bash scripting. We will update the system, install the UFW (Uncomplicated Firewall), allow SSH connections, enable the firewall, and display the firewall status.
#!/bin/bash
# Update system
sudo apt-get update -y
# Install UFW Firewall
sudo apt-get install ufw -y
# Allow SSH Connections
sudo ufw allow ssh
# Enable Firewall
sudo ufw enable
# Display Firewall Status
sudo ufw status verboseThis script provides a basic level of security for your Linux system. However, remember that cybersecurity is a continuous process and requires regular updates and checks. Always keep your system updated and monitor your firewall status regularly.

Level Up! Linux Tools to Boost Your Cybersecurity Game 🛠️
Top Linux Tools for Cybersecurity
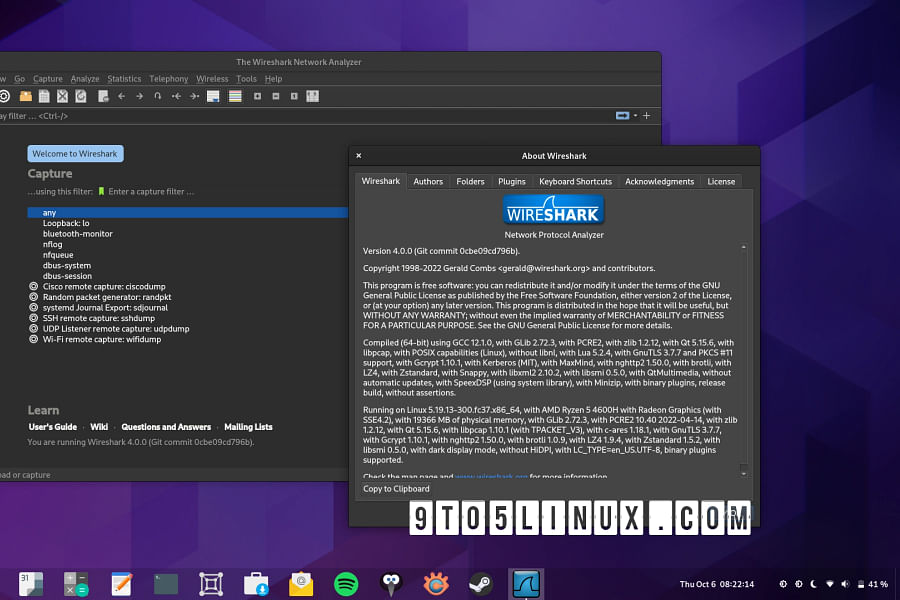
- Wireshark - A network protocol analyzer that lets you capture and interactively browse the traffic running on a computer network.
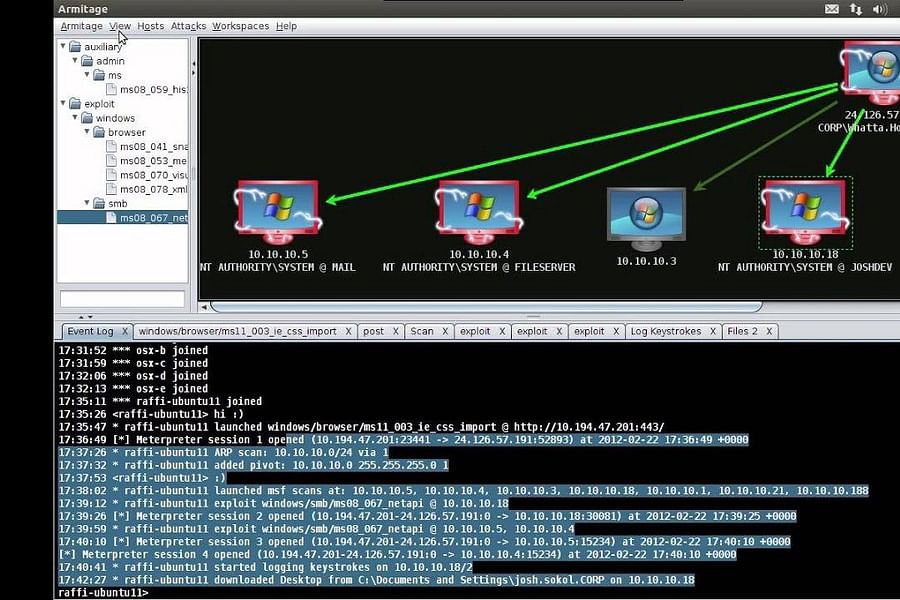
- Metasploit - A penetration testing framework that makes hacking simple. It's used by cybersecurity professionals to detect vulnerabilities.
- Nmap - A network mapper tool that uses IP packets to identify all devices on a network, what services they offer, and details about their operating system and other software.
- John the Ripper - A fast password cracker, currently available for many flavors of Unix, Windows, DOS, and OpenVMS.

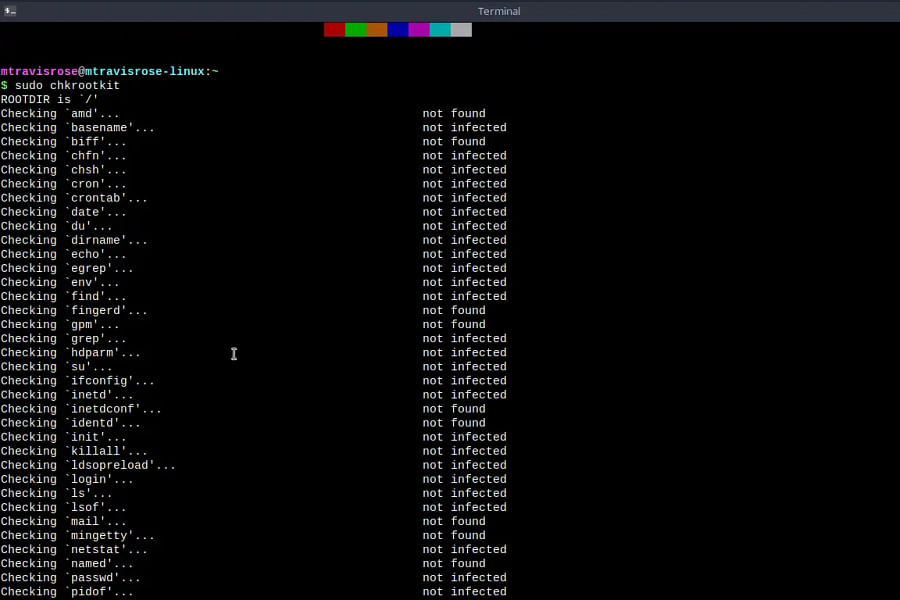
- Chkrootkit - A tool to locally check for signs of a rootkit. It contains a string of utilities that can detect various malicious software.
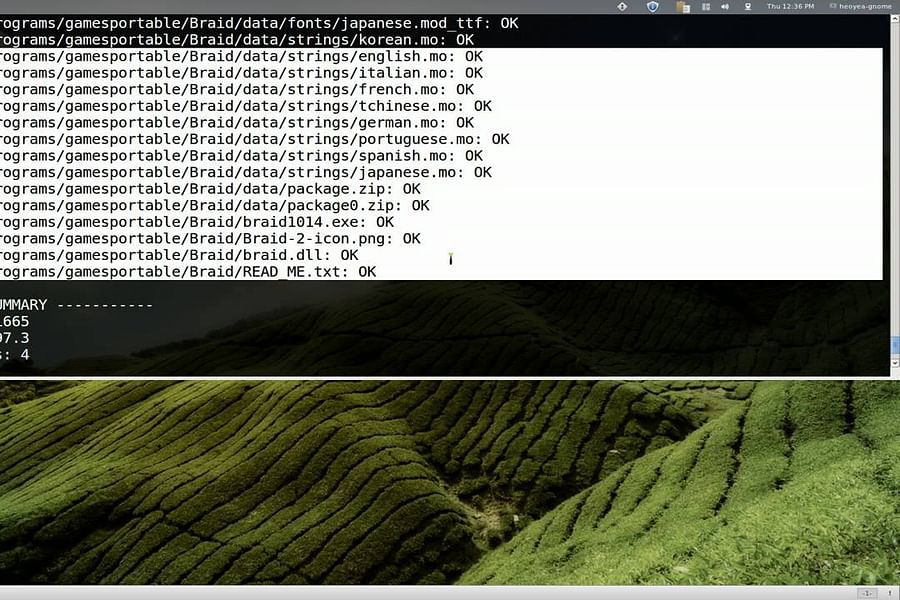
- ClamAV - An open source antivirus engine for detecting trojans, viruses, malware & other malicious threats.
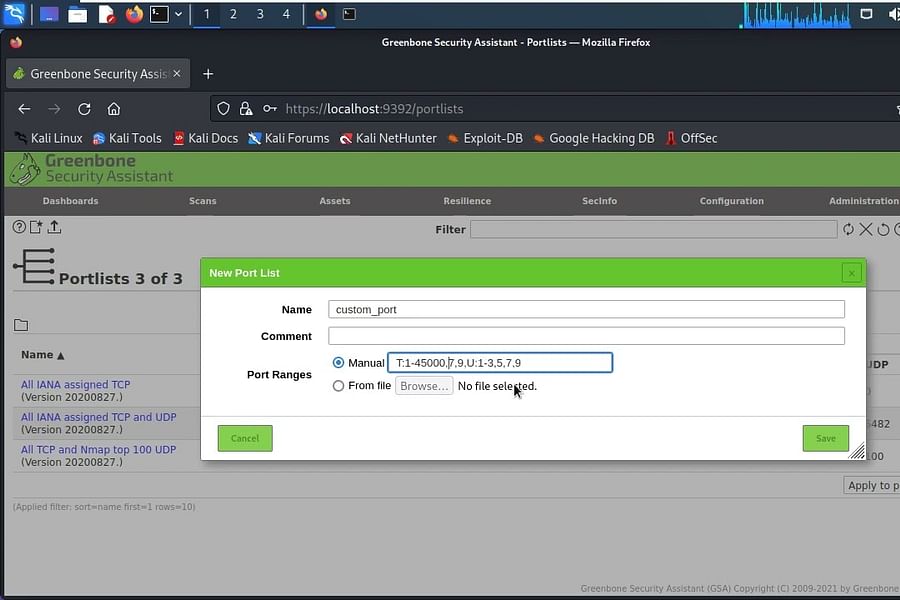
- OpenVAS - A full-featured vulnerability scanner. Its capabilities include unauthenticated testing, authenticated testing, various high level and low level Internet and industrial protocols.
Now that we've discussed the various tools and applications available for enhancing cybersecurity in Linux, let's take a closer look at how to use some of them. Here's a comprehensive tutorial on vulnerability scanning with Nmap and Metasploit:
That was an in-depth look at how to use Nmap and Metasploit for vulnerability scanning. These tools, along with the other ones mentioned earlier, can greatly enhance your cybersecurity capabilities when using Linux. Now, let's wrap up our discussion on mastering cybersecurity with Linux.
Your Journey to Mastering Cybersecurity with Linux: Keep Learning, Keep Growing 🌱
And there you have it, my dear reader, the comprehensive Linux cybersecurity roadmap right at your fingertips. But remember, mastering Linux security and hardening isn't a sprint, it's a marathon. A never-ending marathon that requires your consistent dedication and enthusiasm. Why is Linux important to learn for cyber security, you ask? Well, it's like asking, why should a swordsman sharpen his blade? Linux isn't just a tool, it's the weapon with which you'll vanquish your cyber foes.
Make no mistake, the landscape of cyber threat is as dynamic as it is treacherous. Yesterday's safe haven might become today's hunting ground. That's why it's crucial to stay updated and keep evolving. The best Linux distros for cybersecurity aren't stagnant, they're perpetually upgraded, always ready to combat new threats.
So, are you ready to embark on this thrilling journey of mastering cybersecurity with Linux? Are you prepared to wield the power of Linux cybersecurity tools to safeguard the digital realm? The world is waiting for heroes like you, ready to brave the storm. Go ahead, let your journey begin. Until next time, remember - the key to mastering cybersecurity is not just knowledge, but the relentless pursuit of it.
Mastering Cybersecurity with Linux Quiz
Test your understanding of the article 'Mastering Cybersecurity with Linux Distros: A Comprehensive Guide for Beginners'.
Learn more about 🔐 Mastering Cybersecurity with Linux Quiz or discover other Guide Techy quizzes.












No comments yet. Be the first to share your thoughts!